
Introduction
OAuth 2.0 was published in 2012. In the fourteen years since, the security landscape has changed so dramatically that three of its original grant types are now considered dangerous. Implicit grant, which skipped the authorization code exchange and put tokens directly in browser URLs, was a pragmatic shortcut for single-page applications that couldn't keep secrets. Resource Owner Password Credentials (ROPC), which asked users to hand their passwords directly to third-party apps, was a bridge for legacy systems migrating from Basic Auth. Both were reasonable compromises at the time. Both are attack vectors today.
OAuth 2.1 is not a revolution. It is a consolidation. The IETF took the best practices that emerged from years of security research, incident postmortems, and RFC extensions — PKCE, refresh token rotation, stricter redirect URI matching — and folded them into a single specification that replaces OAuth 2.0. If you've been following security best practices, you're probably already doing most of what OAuth 2.1 requires. If you haven't, this is your wake-up call.
The timing matters because 2026 is the year machine-to-machine authentication overtook human-to-service authentication in volume. AI agents, microservices, CI/CD pipelines, and IoT devices now generate more API traffic than browser-based users. The Client Credentials flow — the grant type designed for machines — has become the most important flow to get right. And the patterns for securing tokens, rotating credentials, and validating claims have evolved significantly since the last time most teams reviewed their auth stack.
This post walks through everything an intermediate developer needs to understand and implement OAuth 2.1 correctly. We'll cover what changed from 2.0 and why, break down PKCE so it actually makes sense, implement production-ready auth in both Python (FastAPI) and TypeScript (Node.js), compare JWT against opaque tokens with a clear decision framework, and catalog the security anti-patterns that still plague production systems. By the end, you'll have both the conceptual understanding and the working code to secure your APIs properly.
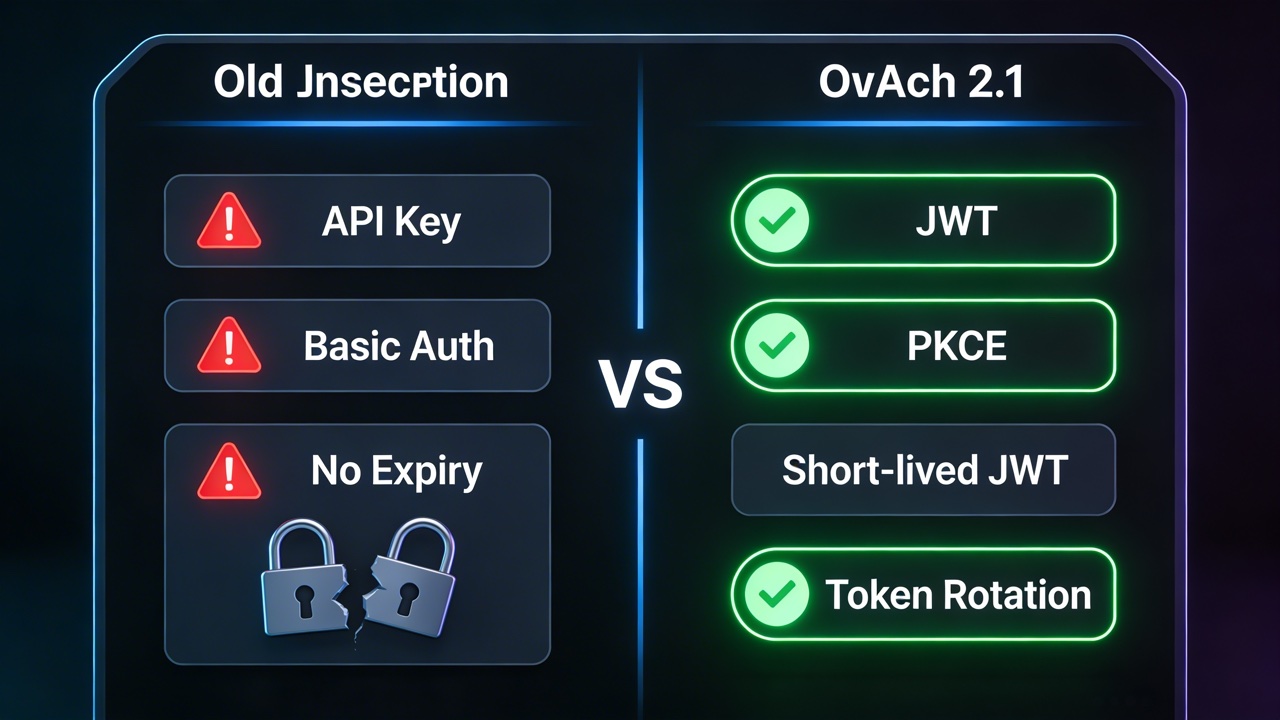
The Problem: Broken Auth Patterns That Won't Die

Every major API breach in the past three years traces back to one of a handful of authentication failures. Not exotic zero-days. Not nation-state tooling. Broken auth. The kind of vulnerabilities that exist because teams copied a tutorial from 2016 and never revisited their implementation.
The Implicit Grant Disaster
The implicit grant was designed for browser-based JavaScript applications that couldn't securely store a client secret. Instead of exchanging an authorization code for tokens at a token endpoint, the authorization server returned the access token directly in the URL fragment. The logic was simple: the fragment isn't sent to the server, so it's "safe enough."
It wasn't. Access tokens in URL fragments get logged in browser history, leaked via the Referer header, captured by browser extensions, and exposed to any JavaScript running on the page. A single XSS vulnerability turns implicit grant tokens into a credential-harvesting bonanza. The token has no binding to the client that requested it, so a stolen token works anywhere. There is no refresh token, so access tokens must be long-lived — widening the attack window from minutes to hours.
OAuth 2.1 removes the implicit grant entirely. Every client, including single-page applications, must use the authorization code flow with PKCE.
Resource Owner Password Credentials: Trust Nobody
ROPC asked users to type their username and password directly into the third-party application, which then sent those credentials to the authorization server. This required users to trust that the application wouldn't store, leak, or misuse their raw credentials. It trained users to enter passwords into apps that aren't the identity provider — the exact behavior that phishing attacks exploit.
OAuth 2.1 removes ROPC entirely. There is no legitimate use case for a third-party application to handle user passwords in 2026.
Token Sprawl and Leaked Secrets
Beyond deprecated flows, production systems suffer from endemic token management failures. Long-lived API keys committed to Git repositories. Refresh tokens stored in localStorage where any XSS payload can exfiltrate them. Access tokens with 24-hour lifetimes because "the refresh logic was too complicated." Service accounts with wildcard permissions because scoping was "too much work for the sprint."
A 2025 study of GitHub public repositories found over 12 million leaked API credentials — tokens, keys, and secrets exposed in source code. Secret scanning helps after the fact, but the root problem is architectural: teams treat authentication as a configuration checkbox rather than a security boundary.
The Machine Identity Gap
The fastest-growing attack surface is machine-to-machine authentication. Microservices calling microservices. AI agents calling APIs. Pipelines calling deployment targets. Most teams handle this with static API keys or long-lived service account tokens — the exact pattern that turns a single compromised service into lateral movement across the entire system.
OAuth 2.1's Client Credentials flow, combined with short-lived tokens and certificate-bound credentials, addresses this gap. But only if you implement it correctly.
*Figure 1: OAuth 2.0's deprecated flows (implicit grant and ROPC) create multiple attack vectors. OAuth 2.1 mandates the authorization code flow with PKCE for all clients.*
How It Works: OAuth 2.1 Core Changes and the PKCE Flow
OAuth 2.1 doesn't introduce new grant types. It removes dangerous ones, mandates security extensions that were optional in 2.0, and tightens the rules for everything that remains. Here are the key changes.
What OAuth 2.1 Removes
Implicit grant is gone. No more response_type=token. All clients use the authorization code flow, including single-page applications and mobile apps. If your SPA currently uses implicit grant, migration is mandatory.
Resource Owner Password Credentials is gone. No more sending usernames and passwords through third-party applications. First-party apps that need password-based login should use the authorization code flow with a first-party authorization server.
What OAuth 2.1 Mandates
PKCE is required for every authorization code flow, not just public clients. In OAuth 2.0, PKCE was recommended for mobile and SPA clients but optional for confidential (server-side) clients. OAuth 2.1 requires PKCE universally. This protects against authorization code interception attacks even for server-side applications.
Exact redirect URI matching replaces pattern matching. In OAuth 2.0, some authorization servers allowed wildcard or prefix matching on redirect URIs (e.g., https://app.example.com/*). OAuth 2.1 requires exact string matching. The redirect URI in the authorization request must exactly match one of the registered redirect URIs for the client.
Refresh token rotation or sender-constraining is required. Every time a refresh token is used, the authorization server must either issue a new refresh token (rotation) or bind the refresh token to the client via mTLS or DPoP (sender-constraining). Stolen refresh tokens can't be replayed indefinitely.
PKCE: How It Actually Works
PKCE (Proof Key for Code Exchange, pronounced "pixie") solves a specific problem: what happens if an attacker intercepts the authorization code during the redirect back to the client? Without PKCE, the attacker can exchange that code for tokens at the token endpoint. With PKCE, only the client that initiated the request can complete the exchange.
Here's the flow step by step:
Step 1: Client generates a random secret. The client creates a cryptographically random string called the code_verifier. This is a high-entropy string between 43 and 128 characters.
Step 2: Client derives a challenge. The client computes the SHA-256 hash of the code_verifier and base64url-encodes it. This is the code_challenge.
Step 3: Client sends the challenge with the authorization request. The authorization request includes code_challenge and code_challenge_method=S256. The authorization server stores this challenge.
Step 4: User authenticates and authorization server redirects with a code. Standard OAuth behavior — the user logs in, consents, and the server redirects to the client's redirect URI with an authorization code.
Step 5: Client exchanges the code with the original verifier. The token request includes both the authorization code and the original code_verifier. The authorization server hashes the verifier, compares it to the stored challenge, and only issues tokens if they match.
An attacker who intercepts the authorization code in Step 4 cannot complete Step 5 because they don't have the code_verifier. The code_challenge sent in Step 3 is a one-way hash — you can't reverse it to get the verifier.
&code_challenge=abc123
&code_challenge_method=S256
&client_id=...&redirect_uri=...&scope=... AuthServer->>User: Login page User->>AuthServer: Authenticate + consent AuthServer->>Client: Redirect to redirect_uri?code=AUTH_CODE Note over Client: Attacker may intercept AUTH_CODE here
but cannot proceed without code_verifier Client->>AuthServer: POST /token
code=AUTH_CODE
&code_verifier=original_secret
&client_id=...&redirect_uri=... Note over AuthServer: Verify: SHA256(code_verifier) == stored code_challenge AuthServer->>Client: { access_token, refresh_token, expires_in } style Client fill:#3b82f6 style AuthServer fill:#8b5cf6 style User fill:#22c55e
*Figure 2: The PKCE authorization code flow. The code_verifier never leaves the client until the token exchange, preventing authorization code interception attacks.*
Token Lifecycle in OAuth 2.1
OAuth 2.1 tightens the entire token lifecycle:
Access tokens should be short-lived: 5-15 minutes is the recommended range. Short lifetimes limit the damage window if a token is stolen. The trade-off is more frequent refresh operations, but modern HTTP clients handle this transparently.
Refresh tokens must be rotated or sender-constrained. Rotation means every refresh request returns a new refresh token, and the old one is invalidated. If an attacker steals a refresh token and the legitimate client also uses it, the authorization server detects the reuse and revokes the entire token family.
Token binding (via DPoP or mTLS) ties tokens to a specific client's cryptographic key. Even if a bound token is intercepted, it can't be used from a different machine because the attacker doesn't have the private key. DPoP (Demonstration of Proof-of-Possession) is the most practical binding mechanism for web applications.
Implementation Guide: Production Code in Python and TypeScript
Let's build production-ready OAuth 2.1 implementations. We'll cover the authorization code flow with PKCE for user-facing apps and the Client Credentials flow for machine-to-machine auth.
Python (FastAPI): OAuth 2.1 Authorization Server Middleware
This middleware validates incoming access tokens, supports both JWT and opaque token introspection, and enforces scope-based access control.
# oauth_middleware.py — FastAPI OAuth 2.1 Token Validation
import hashlib
import secrets
import time
from datetime import datetime, timedelta, timezone
from typing import Optional
import httpx
from fastapi import Depends, FastAPI, HTTPException, Request, Security
from fastapi.security import HTTPAuthorizationCredentials, HTTPBearer
from jose import JWTError, jwt
from pydantic import BaseModel
app = FastAPI()
security = HTTPBearer()
# Configuration — load from environment in production
JWKS_URI = "https://auth.example.com/.well-known/jwks.json"
ISSUER = "https://auth.example.com"
AUDIENCE = "https://api.example.com"
INTROSPECTION_ENDPOINT = "https://auth.example.com/oauth/introspect"
CLIENT_ID = "api-server"
CLIENT_SECRET = "server-secret" # Use env var in production
# JWKS cache with TTL
_jwks_cache: dict = {"keys": [], "expires_at": 0}
async def get_jwks() -> dict:
"""Fetch and cache JWKS (JSON Web Key Set) from the authorization server."""
now = time.time()
if _jwks_cache["expires_at"] > now:
return _jwks_cache
async with httpx.AsyncClient() as client:
response = await client.get(JWKS_URI, timeout=5.0)
response.raise_for_status()
keys = response.json()
_jwks_cache["keys"] = keys.get("keys", [])
_jwks_cache["expires_at"] = now + 3600 # Cache for 1 hour
return _jwks_cache
class TokenClaims(BaseModel):
"""Validated token claims available to route handlers."""
sub: str
scope: list[str]
client_id: Optional[str] = None
exp: int
iss: str
aud: str
async def validate_jwt_token(token: str) -> TokenClaims:
"""Validate a JWT access token against the authorization server's JWKS."""
try:
jwks = await get_jwks()
# Decode header to find the key ID (kid)
unverified_header = jwt.get_unverified_header(token)
kid = unverified_header.get("kid")
# Find matching key in JWKS
rsa_key = None
for key in jwks["keys"]:
if key.get("kid") == kid:
rsa_key = key
break
if not rsa_key:
raise HTTPException(status_code=401, detail="Token signing key not found")
# Verify token signature, expiration, issuer, and audience
payload = jwt.decode(
token,
rsa_key,
algorithms=["RS256"],
audience=AUDIENCE,
issuer=ISSUER,
options={"require_exp": True, "require_iss": True, "require_aud": True},
)
# Parse scope — OAuth 2.1 uses space-delimited scope string
scope_str = payload.get("scope", "")
scopes = scope_str.split() if isinstance(scope_str, str) else scope_str
return TokenClaims(
sub=payload["sub"],
scope=scopes,
client_id=payload.get("client_id"),
exp=payload["exp"],
iss=payload["iss"],
aud=payload["aud"],
)
except JWTError as e:
raise HTTPException(
status_code=401,
detail=f"Invalid token: {str(e)}",
headers={"WWW-Authenticate": "Bearer"},
)
async def validate_opaque_token(token: str) -> TokenClaims:
"""Validate an opaque token via the introspection endpoint (RFC 7662)."""
async with httpx.AsyncClient() as client:
response = await client.post(
INTROSPECTION_ENDPOINT,
data={"token": token, "token_type_hint": "access_token"},
auth=(CLIENT_ID, CLIENT_SECRET),
timeout=5.0,
)
response.raise_for_status()
data = response.json()
if not data.get("active"):
raise HTTPException(
status_code=401,
detail="Token is inactive or revoked",
headers={"WWW-Authenticate": "Bearer"},
)
scope_str = data.get("scope", "")
scopes = scope_str.split() if isinstance(scope_str, str) else scope_str
return TokenClaims(
sub=data["sub"],
scope=scopes,
client_id=data.get("client_id"),
exp=data["exp"],
iss=data.get("iss", ISSUER),
aud=data.get("aud", AUDIENCE),
)
async def get_current_token(
credentials: HTTPAuthorizationCredentials = Security(security),
) -> TokenClaims:
"""Extract and validate the bearer token from the Authorization header.
Automatically detects JWT vs opaque tokens. JWTs contain dots (header.payload.signature),
opaque tokens do not.
"""
token = credentials.credentials
if token.count(".") == 2:
# Looks like a JWT — validate locally using JWKS
return await validate_jwt_token(token)
else:
# Opaque token — validate via introspection
return await validate_opaque_token(token)
def require_scope(required: str):
"""Dependency that enforces a specific OAuth scope on the endpoint."""
async def check_scope(claims: TokenClaims = Depends(get_current_token)):
if required not in claims.scope:
raise HTTPException(
status_code=403,
detail=f"Insufficient scope. Required: {required}",
)
return claims
return check_scope
# --- PKCE Helper: Client-side code verifier and challenge generation ---
def generate_pkce_pair() -> tuple[str, str]:
"""Generate a PKCE code_verifier and code_challenge pair.
Returns:
Tuple of (code_verifier, code_challenge) where the challenge
is the base64url-encoded SHA-256 hash of the verifier.
"""
# Generate 32 bytes of random data, base64url-encode to get 43 chars
code_verifier = secrets.token_urlsafe(32)
# Compute S256 challenge: BASE64URL(SHA256(code_verifier))
digest = hashlib.sha256(code_verifier.encode("ascii")).digest()
code_challenge = (
__import__("base64")
.urlsafe_b64encode(digest)
.rstrip(b"=")
.decode("ascii")
)
return code_verifier, code_challenge
# --- Example Protected Routes ---
@app.get("/api/user/profile")
async def get_profile(claims: TokenClaims = Depends(require_scope("profile:read"))):
"""Protected endpoint requiring 'profile:read' scope."""
return {
"user_id": claims.sub,
"scopes": claims.scope,
"token_expires": datetime.fromtimestamp(claims.exp, tz=timezone.utc).isoformat(),
}
@app.post("/api/data/export")
async def export_data(claims: TokenClaims = Depends(require_scope("data:export"))):
"""Protected endpoint requiring 'data:export' scope."""
return {
"status": "export_started",
"requested_by": claims.sub,
"client_id": claims.client_id,
}
TypeScript (Node.js): Client Credentials Flow for Machine-to-Machine Auth
This implementation handles the Client Credentials flow for service-to-service authentication, with automatic token refresh and retry logic.
// oauth-client.ts — Machine-to-Machine OAuth 2.1 Client
import crypto from "crypto";
interface TokenResponse {
access_token: string;
token_type: string;
expires_in: number;
scope?: string;
}
interface CachedToken {
accessToken: string;
expiresAt: number; // Unix timestamp in milliseconds
scopes: string[];
}
interface OAuthClientConfig {
tokenEndpoint: string;
clientId: string;
clientSecret: string;
defaultScopes: string[];
// Buffer in seconds before expiry to trigger refresh (default: 30)
refreshBuffer?: number;
}
class OAuthClientCredentials {
private config: OAuthClientConfig;
private tokenCache: CachedToken | null = null;
private pendingRefresh: Promise<CachedToken> | null = null;
constructor(config: OAuthClientConfig) {
this.config = config;
}
/**
* Get a valid access token, refreshing if necessary.
* Uses a single-flight pattern to prevent concurrent token requests.
*/
async getToken(scopes?: string[]): Promise<string> {
const requestedScopes = scopes ?? this.config.defaultScopes;
// Check if cached token is still valid
if (this.tokenCache && this.isTokenValid(this.tokenCache)) {
// Verify cached token has all requested scopes
const hasAllScopes = requestedScopes.every((s) =>
this.tokenCache!.scopes.includes(s)
);
if (hasAllScopes) {
return this.tokenCache.accessToken;
}
}
// Single-flight: if a refresh is already in progress, wait for it
if (this.pendingRefresh) {
const token = await this.pendingRefresh;
return token.accessToken;
}
// Fetch a new token
this.pendingRefresh = this.fetchToken(requestedScopes);
try {
const token = await this.pendingRefresh;
this.tokenCache = token;
return token.accessToken;
} finally {
this.pendingRefresh = null;
}
}
/**
* Make an authenticated HTTP request with automatic token management.
* Retries once on 401 with a fresh token.
*/
async authenticatedFetch(
url: string,
options: RequestInit = {}
): Promise<Response> {
const token = await this.getToken();
const headers = new Headers(options.headers);
headers.set("Authorization", `Bearer ${token}`);
let response = await fetch(url, { ...options, headers });
// If 401, token might have been revoked — get fresh token and retry once
if (response.status === 401) {
this.tokenCache = null; // Invalidate cache
const freshToken = await this.getToken();
headers.set("Authorization", `Bearer ${freshToken}`);
response = await fetch(url, { ...options, headers });
}
return response;
}
private isTokenValid(token: CachedToken): boolean {
const bufferMs = (this.config.refreshBuffer ?? 30) * 1000;
return Date.now() < token.expiresAt - bufferMs;
}
private async fetchToken(scopes: string[]): Promise<CachedToken> {
// Build the token request per OAuth 2.1 Client Credentials flow
const body = new URLSearchParams({
grant_type: "client_credentials",
scope: scopes.join(" "),
});
// Client authentication via HTTP Basic (client_id:client_secret)
const credentials = Buffer.from(
`${this.config.clientId}:${this.config.clientSecret}`
).toString("base64");
const response = await fetch(this.config.tokenEndpoint, {
method: "POST",
headers: {
"Content-Type": "application/x-www-form-urlencoded",
Authorization: `Basic ${credentials}`,
},
body: body.toString(),
});
if (!response.ok) {
const errorBody = await response.text();
throw new Error(
`Token request failed (${response.status}): ${errorBody}`
);
}
const data: TokenResponse = await response.json();
return {
accessToken: data.access_token,
expiresAt: Date.now() + data.expires_in * 1000,
scopes: data.scope?.split(" ") ?? scopes,
};
}
}
// --- PKCE Utilities for Browser/Mobile Clients ---
function generateCodeVerifier(): string {
// 32 bytes of random data, base64url-encoded
const buffer = crypto.randomBytes(32);
return buffer
.toString("base64")
.replace(/\+/g, "-")
.replace(/\//g, "_")
.replace(/=/g, "");
}
async function generateCodeChallenge(verifier: string): Promise<string> {
const encoder = new TextEncoder();
const data = encoder.encode(verifier);
const digest = await crypto.subtle.digest("SHA-256", data);
return Buffer.from(digest)
.toString("base64")
.replace(/\+/g, "-")
.replace(/\//g, "_")
.replace(/=/g, "");
}
// --- Usage Example ---
async function main() {
// Machine-to-machine: service calling another service
const authClient = new OAuthClientCredentials({
tokenEndpoint: "https://auth.example.com/oauth/token",
clientId: "data-pipeline-service",
clientSecret: process.env.OAUTH_CLIENT_SECRET!,
defaultScopes: ["data:read", "data:write"],
refreshBuffer: 60, // Refresh 60 seconds before expiry
});
// Automatic token management — get token, cache, refresh transparently
const response = await authClient.authenticatedFetch(
"https://api.example.com/v1/data/process",
{
method: "POST",
headers: { "Content-Type": "application/json" },
body: JSON.stringify({ pipeline: "daily-etl", batch_size: 1000 }),
}
);
console.log("API response:", response.status, await response.json());
// PKCE for user-facing auth flows
const codeVerifier = generateCodeVerifier();
const codeChallenge = await generateCodeChallenge(codeVerifier);
console.log("PKCE verifier:", codeVerifier);
console.log("PKCE challenge:", codeChallenge);
}
main().catch(console.error);
Refresh Token Rotation with Replay Detection
Here is a standalone FastAPI endpoint that demonstrates refresh token rotation with replay detection — critical for preventing stolen refresh tokens from being reused.
# refresh_rotation.py — Refresh Token Rotation with Replay Detection
import secrets
import time
from dataclasses import dataclass, field
from fastapi import FastAPI, HTTPException
from pydantic import BaseModel
app = FastAPI()
@dataclass
class TokenFamily:
"""Tracks a chain of refresh tokens from a single authorization grant.
If any token in the family is reused after rotation, the entire
family is revoked — this detects token theft.
"""
family_id: str
current_token_hash: str
user_id: str
scopes: list[str]
created_at: float
rotated_at: float
used_tokens: set[str] = field(default_factory=set) # Hashes of already-rotated tokens
revoked: bool = False
# In production, use Redis or a database — not an in-memory dict
token_families: dict[str, TokenFamily] = {} # family_id -> TokenFamily
token_to_family: dict[str, str] = {} # token_hash -> family_id
def hash_token(token: str) -> str:
"""Hash a refresh token for storage. Never store raw refresh tokens."""
import hashlib
return hashlib.sha256(token.encode()).hexdigest()
class RefreshRequest(BaseModel):
refresh_token: str
client_id: str
class TokenPair(BaseModel):
access_token: str
refresh_token: str
token_type: str = "Bearer"
expires_in: int = 900 # 15 minutes
@app.post("/oauth/token/refresh", response_model=TokenPair)
async def refresh_token(request: RefreshRequest) -> TokenPair:
"""Exchange a refresh token for a new access + refresh token pair.
Implements refresh token rotation per OAuth 2.1:
1. Each refresh generates a new refresh token
2. The old refresh token is invalidated
3. If a previously-rotated token is reused, the ENTIRE family is revoked
(indicates the token was stolen and both parties are trying to use it)
"""
token_hash = hash_token(request.refresh_token)
# Look up which token family this refresh token belongs to
family_id = token_to_family.get(token_hash)
if not family_id:
raise HTTPException(status_code=401, detail="Invalid refresh token")
family = token_families.get(family_id)
if not family:
raise HTTPException(status_code=401, detail="Token family not found")
# Check if family is already revoked
if family.revoked:
raise HTTPException(
status_code=401,
detail="Token family revoked due to suspected theft. Re-authenticate.",
)
# REPLAY DETECTION: Is this a previously-used token?
if token_hash in family.used_tokens:
# This token was already rotated — someone is replaying it.
# Revoke the entire family to protect the user.
family.revoked = True
raise HTTPException(
status_code=401,
detail="Refresh token reuse detected. All tokens revoked. Re-authenticate.",
)
# Verify this is the current (most recent) refresh token
if token_hash != family.current_token_hash:
# Not the current token and not in used_tokens — shouldn't happen
family.revoked = True
raise HTTPException(status_code=401, detail="Token family compromised")
# --- Rotation: issue new tokens ---
# Move current token to used set
family.used_tokens.add(token_hash)
# Generate new refresh token
new_refresh_token = secrets.token_urlsafe(48)
new_token_hash = hash_token(new_refresh_token)
# Update family
family.current_token_hash = new_token_hash
family.rotated_at = time.time()
# Update lookup index
token_to_family[new_token_hash] = family_id
# Optionally remove old mapping after a grace period (not immediately,
# in case of network retries)
# Generate new access token (in production, sign a JWT)
new_access_token = secrets.token_urlsafe(32)
return TokenPair(
access_token=new_access_token,
refresh_token=new_refresh_token,
)
Comparison and Tradeoffs: JWT vs Opaque Tokens, API Keys vs OAuth
Choosing the right token format and authentication mechanism is one of the most consequential architectural decisions in API design. There is no universal best choice — the right answer depends on your system's specific requirements.
JWT vs Opaque Tokens
| Aspect | JWT (Self-contained) | Opaque Tokens (Reference) |
|--------|---------------------|--------------------------|
| Validation | Local — verify signature and claims | Remote — call introspection endpoint |
| Latency | No network call needed | Adds 1-5ms per request for introspection |
| Revocation | Difficult — token is valid until expiry | Immediate — delete from server store |
| Size | 800-2000+ bytes (grows with claims) | 32-48 bytes (fixed) |
| Privacy | Claims visible to anyone with the token | Claims only visible to authorization server |
| Scalability | Excellent — no shared state | Requires fast introspection backend (Redis) |
| Debugging | Easy — decode at jwt.io | Need server access to inspect |
| Best for | Microservices, distributed systems | User-facing apps needing instant revocation |
Use JWTs when you need stateless validation at scale across many services and can tolerate the revocation delay (keep access token lifetime under 15 minutes). JWTs shine in microservice architectures where dozens of services need to validate tokens independently.
Use opaque tokens when you need instant revocation (financial services, healthcare), want to keep claims private, or have a centralized API gateway that can handle introspection efficiently.
API Keys vs OAuth
API keys are not an authentication standard. They are shared secrets. Treating them as equivalent to OAuth is a category error that persists across the industry.
| Aspect | API Keys | OAuth 2.1 Client Credentials |
|--------|----------|------------------------------|
| Rotation | Manual — requires app redeployment | Automatic — short-lived tokens |
| Scope | Typically all-or-nothing | Fine-grained per-request scopes |
| Revocation | Regenerate key, update all clients | Revoke grant, tokens expire naturally |
| Audit trail | Key identified, not action context | Full token introspection with metadata |
| Credential exposure | Single static secret in config | Client secret exchanges for ephemeral tokens |
| Best for | Rate limiting, usage tracking | Authentication and authorization |
Use API keys for identifying callers (metering, rate limiting, analytics). API keys answer "who is calling?" but should not answer "what are they allowed to do?"
Use OAuth Client Credentials for authorizing actions. Short-lived tokens, scoped permissions, and automatic rotation make this the correct choice for machine-to-machine authentication.
mTLS for High-Security Environments
Mutual TLS (mTLS) adds certificate-based client authentication at the transport layer. The client presents a certificate during the TLS handshake, and the server verifies it against a trusted CA. This provides the strongest client authentication but requires certificate management infrastructure (issuance, rotation, revocation lists).
Use mTLS when operating in zero-trust environments, securing service meshes, or meeting regulatory requirements (PCI-DSS, SOC 2). Combine with OAuth for defense in depth: mTLS authenticates the transport, OAuth authorizes the action.
*Figure 3: Decision framework for choosing the right authentication pattern. The choice depends on who is authenticating (human vs machine), the client type, and security requirements.*
Production Considerations
Token Storage by Client Type
Where you store tokens determines your security posture. There is no single correct answer — it depends on your client architecture.
Server-side applications: Store tokens in server-side sessions (Redis, database). Tokens never reach the browser. This is the most secure option and the reason confidential clients exist.
Single-page applications: Use the Backend-for-Frontend (BFF) pattern. The SPA talks to a thin backend that holds tokens in HTTP-only, Secure, SameSite=Strict cookies. The SPA never directly handles access or refresh tokens. Storing tokens in localStorage or sessionStorage exposes them to XSS attacks.
Mobile applications: Use platform-specific secure storage — iOS Keychain or Android Keystore. These provide hardware-backed encryption that survives app restarts. Never store tokens in SharedPreferences, UserDefaults, or any plaintext storage.
CLI tools and agents: Use the system keychain (macOS Keychain, Windows Credential Manager, Linux Secret Service) via libraries like keyring (Python) or keytar (Node.js). For CI/CD environments, use the platform's secrets manager (GitHub Actions secrets, AWS Secrets Manager).
Monitoring and Alerting
OAuth infrastructure generates high-value security signals. Monitor these actively:
Token issuance rate: A sudden spike in token requests from a single client may indicate credential compromise or a misconfigured retry loop. Set alerts for rates exceeding 10x the baseline.
Refresh token reuse: Any reuse of a rotated refresh token is a confirmed security incident. Alert immediately and revoke the token family.
Scope escalation attempts: Clients requesting scopes beyond their registration should trigger security review. This may indicate a compromised client attempting privilege escalation.
Failed introspection rates: A high rate of invalid tokens hitting your introspection endpoint may indicate a brute-force attack or token spray attack.
Authorization code exchange failures: A high rate of PKCE validation failures on the token endpoint may indicate an active authorization code interception attack.
Scaling the Authorization Server
The authorization server is on the critical path for every authenticated request (directly for opaque tokens, indirectly for JWT key rotation). Plan capacity accordingly:
JWKS endpoint caching: Clients should cache the JWKS for hours, not minutes. Set Cache-Control: max-age=3600 on the JWKS endpoint. Key rotation should overlap — publish the new key before signing with it, retire the old key after all cached copies expire.
Introspection endpoint: If using opaque tokens at scale, the introspection endpoint must handle the same request rate as your entire API surface. Back it with Redis or an in-memory cache with sub-millisecond latency.
Rate limiting on token endpoints: Apply strict rate limits on /token and /authorize endpoints. These are authentication endpoints — high request rates are either attacks or misconfigurations.
Common Mistakes and Anti-Patterns
1. Long-lived access tokens (>1 hour): If your access tokens live longer than 15 minutes, you're trading security for convenience. Use refresh tokens instead.
2. Storing tokens in localStorage: XSS attacks can read localStorage. Use the BFF pattern with HTTP-only cookies for browser applications.
3. Skipping PKCE for confidential clients: OAuth 2.1 requires PKCE universally. Even if your server keeps its client secret safe, PKCE protects against authorization code injection attacks at the authorization endpoint level.
4. Hardcoded client secrets in source code: Use environment variables, secret managers, or vault services. Rotate secrets on a schedule, not just when they're compromised.
5. Ignoring token scope: Requesting * or overly broad scopes because "it's easier" violates least privilege. Each client should request the minimum scopes needed for its function.
6. No refresh token rotation: Refresh tokens without rotation are long-lived credentials. If stolen, they grant indefinite access until manually revoked.
7. Using API keys as the sole authentication mechanism: API keys identify callers but don't provide the security properties of OAuth (scoped access, expiration, rotation). Use API keys for metering, OAuth for auth.
8. Validating tokens by calling the authorization server on every request with JWTs: The entire point of JWTs is local validation. If you're calling the authorization server for every JWT, you've built an opaque token system with extra steps. Validate the signature locally.
Conclusion
OAuth 2.1 is not a new standard to learn. It is the formalization of what you should already be doing. PKCE on every authorization code flow. No implicit grant. No ROPC. Refresh token rotation. Short-lived access tokens. Exact redirect URI matching. If any of these are missing from your current implementation, that is the gap to close first.
The decision framework is straightforward: use the authorization code flow with PKCE for human users, Client Credentials for machines, and never use API keys as your sole authentication mechanism. Choose JWTs for distributed validation at scale, opaque tokens when you need instant revocation. Add mTLS when regulations or threat models demand transport-level client authentication.
The code examples in this post are production-ready starting points, not toy demos. The FastAPI middleware handles both JWT and opaque token validation with scope enforcement. The TypeScript client manages the Client Credentials flow with automatic token caching, refresh, and retry logic. The refresh rotation implementation detects token theft through replay detection and revokes the entire token family.
Authentication is not a feature you ship and forget. It is infrastructure that requires ongoing monitoring, rotation, and hardening. Set up alerts for token reuse, scope escalation, and abnormal issuance rates. Review your token lifetimes quarterly. Rotate your client secrets on a schedule. And when OAuth 2.1 is formally ratified — which is expected in late 2026 — you'll already be compliant because you built it right from the start.
If you're building APIs that AI agents consume, revisit our previous post on [API Security in the Age of AI Agents and MCP](https://amtocsoft.blogspot.com/2026/04/api-security-in-age-of-ai-agents-and.html) for the agent-specific threat model. Together, these two posts cover the full authentication and authorization landscape for modern API security.
Enjoyed this post? Follow AmtocSoft for AI tutorials from beginner to professional.
☕ Buy Me a Coffee | 🔔 YouTube | 💼 LinkedIn | 🐦 X/Twitter

No comments:
Post a Comment