Introduction
The identity crisis in modern infrastructure is not about humans forgetting their passwords. It is about the explosive proliferation of non-human actors — AI agents, microservices, CI/CD pipelines, IoT sensors, and automated workflows — that now outnumber human users by a ratio of 45:1 in enterprise API traffic. For every request a developer makes to a production API, forty-five come from machines.
This imbalance has been building for years, but the rise of autonomous AI agents has accelerated it into a full-blown architectural emergency. Traditional identity systems were designed around the assumption that a person sits at the keyboard. They rely on passwords a human can remember, MFA codes a human can receive, and login sessions a human can initiate. None of these primitives translate cleanly to a containerized Python agent that spins up, executes a task, and terminates in under thirty seconds.
The consequences of getting machine identity wrong are severe. In 2023, the CircleCI breach traced back to a single compromised machine identity — a long-lived token with broad access that sat dormant in a developer's environment until an attacker exfiltrated it. In 2024, researchers catalogued over 12 million hardcoded credentials in public GitHub repositories, the overwhelming majority of them machine credentials: API keys, service account tokens, and database passwords embedded directly in source code.
The problem is not that engineers are careless. The problem is that the tooling for machine identity has historically been immature, painful to operate, and poorly integrated with the platforms where modern workloads run. When rotating a certificate requires filing a ticket and waiting three days, engineers reach for a static API key that never expires.
This post is a professional-level deep-dive into machine identity management for AI agent deployments at scale. We will cover the cryptographic foundations — X.509 certificates, SPIFFE IDs, and workload attestation — then move into concrete implementation patterns using SPIRE, Kubernetes projected service account tokens, and HashiCorp Vault dynamic secrets. We will examine tradeoffs across identity strategies, address the operational challenges of managing 10,000+ agent identities, and close with production guidance on monitoring, revocation, and compliance.
If you are building or operating AI agent infrastructure at scale, machine identity is the security primitive you cannot afford to treat as an afterthought.
The Problem: Why Machine Identity Is Broken
The Static Credential Trap
The default path for giving a machine access to a resource is still, in 2026, to generate a static credential and paste it into an environment variable. This approach is understandable — it works immediately, requires no infrastructure, and is familiar to every engineer. It is also a slow-motion security disaster.
Static credentials have four compounding problems. First, they do not expire. A credential issued to a decommissioned agent three years ago may still be valid today, sitting in a rotation's worth of former employees' dotfiles, old CI artifacts, and forgotten S3 buckets. Second, they are hard to scope. Most platforms that issue API keys do so at a coarse level — you get one key per service account, and that key carries all of that account's permissions. Third, they are hard to rotate. In a world where a microservices deployment has 200 services each with 5 credentials, rotation becomes a coordinated effort involving dozens of teams. Fourth, they are easy to leak. Environment variables appear in crash dumps, log aggregators, Docker inspect output, and Kubernetes pod specs that get accidentally committed to version control.
The AI Agent Amplification Effect
AI agents make all of these problems worse by introducing new identity patterns that static credential systems were never designed to handle.
A traditional microservice has a fixed identity: it runs on a known set of hosts, maintains a persistent connection pool, and its traffic patterns are predictable. An AI agent might be ephemeral (spawned on demand, terminated after task completion), dynamic (scaled from zero to thousands of instances based on queue depth), distributed (running across multiple cloud regions and on-premises environments simultaneously), and polyglot (spawning sub-agents in different runtimes that each need their own identities).
The lifecycle of an AI agent identity is fundamentally different from a human identity. There is no onboarding meeting, no IT ticket, no badge photo. An agent needs a valid cryptographic identity within milliseconds of starting, needs that identity to be automatically revoked when it terminates, and needs to be able to prove to every downstream service that it is who it claims to be — without any human in the loop.
The Scale Inflection Point
At small scale — say, fifty agents — you can manage this manually. At 500 agents it becomes painful. At 5,000 agents it becomes impossible. At 50,000 agents, which is not an unrealistic deployment size for enterprises running large-scale AI orchestration platforms, you need a dedicated identity infrastructure that can issue, rotate, and revoke credentials automatically, in real time, without human intervention.
The identity infrastructure must also be resilient. A certificate authority that goes down does not just break authentication — it breaks every agent that needs to renew its credential, which in a short-lived credential system can be every agent in the fleet simultaneously. This is the "certificate storm" problem, and it is one of the most dangerous failure modes in machine identity systems.
Threat Model
The threats that machine identity management must defend against include: credential theft (an attacker obtains a valid credential and uses it to impersonate a legitimate agent), identity spoofing (an attacker creates a fake agent that claims to be a legitimate one), privilege escalation (a compromised agent uses its identity to obtain credentials for resources it should not access), and lateral movement (an attacker pivots from a compromised agent to other parts of the infrastructure by reusing or forging its credentials).
Defending against all of these requires more than just issuing credentials. It requires a system that can attest workload identity (prove that the entity requesting a credential is actually the workload it claims to be), enforce least-privilege scoping, detect anomalous usage patterns, and revoke credentials in real time when a compromise is detected.
How It Works: Cryptographic Identity for Machines
X.509 Certificates and PKI
The foundation of machine identity is Public Key Infrastructure. Each machine gets a unique cryptographic keypair — a private key that never leaves the machine and a public key embedded in an X.509 certificate signed by a trusted Certificate Authority. When two machines communicate, they exchange certificates and verify each other's signatures. This is mutual TLS (mTLS), and it provides three security properties simultaneously: authentication (both parties prove their identity), encryption (the channel is encrypted), and integrity (messages cannot be tampered with in transit).
An X.509 certificate for a machine identity contains several critical fields: the Subject (who this certificate belongs to), the Subject Alternative Names (SANs, which in SPIFFE use a URI format like spiffe://domain/path/workload), the validity period (not before and not after timestamps), the public key, and the issuer's signature. For AI agents, the Subject Alternative Name is the primary identity field — it encodes the workload's logical identity in a format that is independent of IP address, hostname, or ephemeral infrastructure details.
Short-lived certificates are the cornerstone of modern machine identity. Rather than issuing a certificate with a one-year validity period (which gives an attacker a full year to exploit a stolen certificate), modern systems issue certificates with lifetimes of one to twenty-four hours. This dramatically reduces the blast radius of a compromise: a stolen certificate that expires in an hour is a much smaller problem than one that expires in a year.
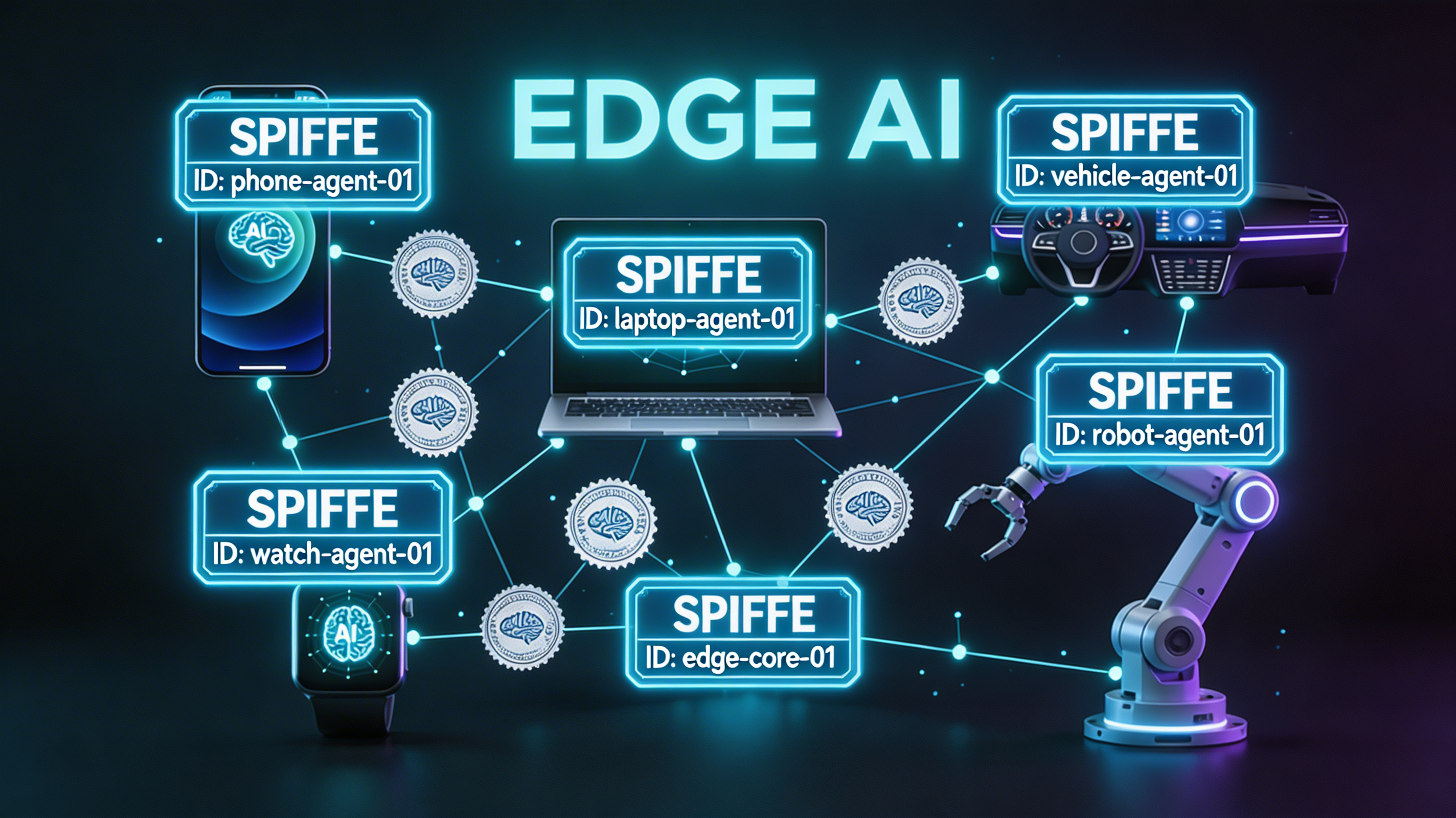
SPIFFE and SPIRE
The Secure Production Identity Framework for Everyone (SPIFFE) is a CNCF standard that defines a universal identity format for workloads, independent of the underlying platform. A SPIFFE ID is a URI of the form spiffe://trust-domain/path — for example, spiffe://payments.corp/agent/invoice-processor/prod. This ID is embedded in an X.509 certificate (called an SVID — SPIFFE Verifiable Identity Document) or a JWT, and can be presented to any workload that trusts the same root CA.
SPIRE (the SPIFFE Runtime Environment) is the reference implementation. It consists of a SPIRE Server (the CA and policy engine) and SPIRE Agents (one per node, acting as a local proxy for workload identity requests). The SPIRE Agent is responsible for workload attestation: when a process requests an SVID, the agent verifies that the process matches a registered workload selector (e.g., "this Kubernetes pod has this service account and runs this container image") before issuing a credential.
Workload Attestation Deep Dive
Workload attestation is the process by which SPIRE proves that a credential request is coming from a legitimate workload rather than an attacker. SPIRE supports multiple attestation plugins depending on the environment.
On Kubernetes, attestation uses the Kubernetes node attestor: the SPIRE Agent running on a node attests itself to the SPIRE Server using the node's bootstrap credentials (typically a kubeconfig tied to the node's service account). The SPIRE Agent then attests individual pods by inspecting their pod specs via the Kubernetes API and matching them against registered workload selectors — things like namespace, service account name, and container image SHA.
On AWS, the node attestor uses the EC2 instance identity document, a signed JSON document that AWS provides to every EC2 instance via the instance metadata service. The SPIRE Server verifies this document's signature against AWS's public key, which proves the node is a real EC2 instance in a specific account and region.
On bare metal or VMs without cloud attestation, TPM-based attestation uses the Trusted Platform Module to produce a signed quote of the machine's state, proving that the software running on the machine has not been tampered with.
JWT SVIDs and Short-Lived Tokens
In addition to X.509 certificates, SPIFFE defines a JWT SVID format for use cases where mTLS is impractical — for example, when an AI agent needs to authenticate to a third-party API that does not support client certificates. A JWT SVID is a signed JWT with the agent's SPIFFE ID in the sub claim and a short expiry (typically 5-60 minutes). The downstream service validates the JWT against SPIRE's JWKS endpoint.
Implementation Guide
1. SPIRE Server Setup and Workload Registration
The following example sets up a SPIRE server, registers a workload, and fetches an SVID using the Python SPIFFE library.
#!/usr/bin/env python3
"""
spire_workload_identity.py
Demonstrates SPIFFE workload identity integration for AI agents.
Requires: pip install pyspiffe grpcio grpcio-tools
Assumes: SPIRE agent running locally with socket at /tmp/spire-agent/public/api.sock
"""
import asyncio
import logging
from datetime import datetime, timezone
from pathlib import Path
from pyspiffe.workloadapi import WorkloadApiClient
from pyspiffe.workloadapi.default_workload_api_client import DefaultWorkloadApiClient
from pyspiffe.bundle.x509_bundle import X509Bundle
from pyspiffe.svid.x509_svid import X509Svid
from pyspiffe.spiffe_id.spiffe_id import SpiffeId
# SPIRE Agent socket — the local proxy for workload identity requests.
# The agent handles attestation; this client just fetches the result.
SPIRE_SOCKET = "unix:///tmp/spire-agent/public/api.sock"
SPIFFE_TRUST_DOMAIN = "payments.corp"
logging.basicConfig(level=logging.INFO, format="%(asctime)s %(levelname)s %(message)s")
log = logging.getLogger(__name__)
class AgentIdentityManager:
"""
Manages the cryptographic identity lifecycle for an AI agent.
Responsibilities:
- Fetch the initial X.509 SVID from SPIRE on startup
- Watch for automatic SVID rotations and update the TLS context
- Provide the current SVID to mTLS connection factories
- Gracefully handle SPIRE unavailability with backoff/retry
"""
def __init__(self, socket_path: str = SPIRE_SOCKET):
self.socket_path = socket_path
self._current_svid: X509Svid | None = None
self._current_bundle: X509Bundle | None = None
self._client: DefaultWorkloadApiClient | None = None
async def initialize(self) -> None:
"""
Connect to the local SPIRE agent and fetch the initial SVID.
Raises RuntimeError if the workload cannot be attested.
"""
log.info("Connecting to SPIRE agent at %s", self.socket_path)
# WorkloadApiClient wraps the gRPC connection to the SPIRE agent.
# The agent performs workload attestation transparently based on
# the calling process's PID, namespace, service account, etc.
self._client = DefaultWorkloadApiClient(workload_api_address=self.socket_path)
try:
# fetch_x509_context returns both the SVID and the trust bundle
# (the set of root CAs needed to verify peer certificates).
context = self._client.fetch_x509_context()
self._current_svid = context.default_svid()
self._current_bundle = context.x509_bundle_set().bundle_for_trust_domain(
SpiffeId.parse(f"spiffe://{SPIFFE_TRUST_DOMAIN}/placeholder").trust_domain
)
self._log_svid_info(self._current_svid)
except Exception as exc:
raise RuntimeError(f"SPIRE attestation failed: {exc}") from exc
def _log_svid_info(self, svid: X509Svid) -> None:
"""Log key fields of the SVID for audit purposes."""
cert = svid.leaf()
not_after = cert.not_valid_after_utc
remaining = not_after - datetime.now(timezone.utc)
log.info(
"SVID issued: spiffe_id=%s not_after=%s remaining=%s",
svid.spiffe_id(),
not_after.isoformat(),
remaining,
)
async def watch_svid_rotation(self) -> None:
"""
Subscribe to SVID rotation events from the SPIRE agent.
SPIRE automatically renews SVIDs before they expire (typically at
the halfway point of the certificate's lifetime). This method runs
indefinitely and updates the cached SVID on each rotation event,
allowing the agent to seamlessly use fresh credentials without restart.
"""
log.info("Starting SVID rotation watcher")
def on_update(context):
"""Called by the SPIRE client each time a new SVID is issued."""
new_svid = context.default_svid()
old_id = str(self._current_svid.spiffe_id()) if self._current_svid else "none"
self._current_svid = new_svid
log.info(
"SVID rotated: old=%s new=%s",
old_id,
new_svid.spiffe_id(),
)
self._log_svid_info(new_svid)
def on_error(error):
"""Called if the SPIRE agent connection fails during a watch."""
log.error("SVID watch error (will retry): %s", error)
# watch_x509_context is a blocking call that fires callbacks on rotation.
# Run it in a thread pool to avoid blocking the event loop.
loop = asyncio.get_event_loop()
await loop.run_in_executor(
None,
lambda: self._client.watch_x509_context(on_update, on_error),
)
@property
def current_svid(self) -> X509Svid | None:
"""Return the current valid SVID, or None if not yet initialized."""
return self._current_svid
def get_tls_credentials(self):
"""
Return a (cert_chain_pem, private_key_pem, trust_bundle_pem) tuple
suitable for constructing a gRPC ssl_channel_credentials object
or an aiohttp SSLContext for outbound mTLS connections.
"""
if not self._current_svid or not self._current_bundle:
raise RuntimeError("Identity not yet initialized — call initialize() first")
cert_chain = b"".join(
cert.public_bytes(encoding=__import__("cryptography.hazmat.primitives.serialization", fromlist=["Encoding"]).Encoding.PEM)
for cert in self._current_svid.cert_chain()
)
private_key = self._current_svid.private_key().private_bytes(
encoding=__import__("cryptography.hazmat.primitives.serialization", fromlist=["Encoding"]).Encoding.PEM,
format=__import__("cryptography.hazmat.primitives.serialization", fromlist=["PrivateFormat"]).PrivateFormat.PKCS8,
encryption_algorithm=__import__("cryptography.hazmat.primitives.serialization", fromlist=["NoEncryption"]).NoEncryption(),
)
trust_bundle = self._current_bundle.serialize_pem()
return cert_chain, private_key, trust_bundle
async def main():
manager = AgentIdentityManager()
await manager.initialize()
# Start the rotation watcher as a background task.
rotation_task = asyncio.create_task(manager.watch_svid_rotation())
# The agent can now use manager.get_tls_credentials() to build
# mTLS connections to downstream services.
log.info("Agent identity ready. SPIFFE ID: %s", manager.current_svid.spiffe_id())
# Keep running to demonstrate rotation.
await asyncio.sleep(7200)
rotation_task.cancel()
if __name__ == "__main__":
asyncio.run(main())
2. Kubernetes Projected Service Account Tokens
Kubernetes 1.24+ supports projected service account tokens — short-lived, audience-scoped JWTs bound to a specific pod. These are the Kubernetes-native equivalent of a SPIFFE JWT SVID.
#!/usr/bin/env python3
"""
k8s_workload_identity.py
Reads and validates a Kubernetes projected service account token for
AI agent authentication to internal APIs.
The token is mounted at /var/run/secrets/kubernetes.io/serviceaccount/token
by the Kubernetes kubelet and is automatically rotated before expiry.
"""
import json
import time
import base64
import logging
from pathlib import Path
from typing import Optional
import httpx # pip install httpx
log = logging.getLogger(__name__)
# Default mount path for projected service account tokens in Kubernetes.
K8S_TOKEN_PATH = Path("/var/run/secrets/kubernetes.io/serviceaccount/token")
K8S_CACERT_PATH = Path("/var/run/secrets/kubernetes.io/serviceaccount/ca.crt")
K8S_NAMESPACE_PATH = Path("/var/run/secrets/kubernetes.io/serviceaccount/namespace")
def read_service_account_token() -> str:
"""
Read the current projected service account token from the filesystem.
Kubernetes automatically rotates this file before the token expires
(default rotation threshold: 80% of token lifetime). Always read
fresh from disk rather than caching in memory to pick up rotations.
"""
if not K8S_TOKEN_PATH.exists():
raise RuntimeError(
f"Service account token not found at {K8S_TOKEN_PATH}. "
"Ensure the pod spec includes the projected service account volume."
)
return K8S_TOKEN_PATH.read_text().strip()
def decode_jwt_claims(token: str) -> dict:
"""
Decode JWT claims without verification (for logging/debugging only).
Never use unverified claims for authorization decisions.
"""
try:
# JWT is header.payload.signature — base64-decode the payload segment.
parts = token.split(".")
# Add padding for base64 decoding.
payload_b64 = parts[1] + "=" * (4 - len(parts[1]) % 4)
payload = json.loads(base64.urlsafe_b64decode(payload_b64))
return payload
except Exception as exc:
log.warning("Could not decode JWT for logging: %s", exc)
return {}
def get_token_expiry_info(token: str) -> tuple[int, int]:
"""
Return (issued_at, expires_at) unix timestamps from a service account token.
Used to proactively rotate before expiry in long-running agents.
"""
claims = decode_jwt_claims(token)
return claims.get("iat", 0), claims.get("exp", 0)
class KubernetesWorkloadIdentity:
"""
Manages Kubernetes projected service account token lifecycle for AI agents.
Unlike static secrets, projected tokens are:
- Audience-scoped (bound to a specific API or service)
- Time-limited (configurable, default 1 hour)
- Pod-bound (invalid if the pod terminates)
- Automatically rotated by the kubelet
"""
def __init__(
self,
token_path: Path = K8S_TOKEN_PATH,
refresh_threshold_seconds: int = 300, # Refresh 5 minutes before expiry.
):
self.token_path = token_path
self.refresh_threshold = refresh_threshold_seconds
self._cached_token: Optional[str] = None
self._token_expiry: int = 0
def get_token(self) -> str:
"""
Return a valid service account token, reading fresh from disk if needed.
Policy: always re-read from disk if the cached token expires within
refresh_threshold_seconds. This ensures we pick up kubelet rotations.
"""
now = int(time.time())
if self._cached_token and self._token_expiry - now > self.refresh_threshold:
return self._cached_token
# Read fresh token from disk (kubelet may have rotated it).
fresh_token = read_service_account_token()
_, expiry = get_token_expiry_info(fresh_token)
self._cached_token = fresh_token
self._token_expiry = expiry
remaining = expiry - now
log.info(
"Service account token loaded: expires_in=%ds namespace=%s",
remaining,
K8S_NAMESPACE_PATH.read_text().strip() if K8S_NAMESPACE_PATH.exists() else "unknown",
)
return self._cached_token
def get_auth_headers(self) -> dict[str, str]:
"""Return Authorization headers for use with HTTP clients."""
return {"Authorization": f"Bearer {self.get_token()}"}
# Example: using the workload identity to call an internal API.
async def call_internal_api(endpoint: str) -> dict:
identity = KubernetesWorkloadIdentity()
async with httpx.AsyncClient(
verify=str(K8S_CACERT_PATH) if K8S_CACERT_PATH.exists() else True,
headers=identity.get_auth_headers(),
timeout=10.0,
) as client:
response = await client.get(endpoint)
response.raise_for_status()
return response.json()
3. HashiCorp Vault Dynamic Secrets
HashiCorp Vault's dynamic secrets engine generates short-lived, unique credentials on demand — database passwords, AWS access keys, API tokens — that are automatically revoked after a configurable TTL.
#!/usr/bin/env python3
"""
vault_dynamic_secrets.py
Demonstrates HashiCorp Vault dynamic secret retrieval for AI agents.
Uses Vault's Kubernetes auth method (no static tokens required).
Requirements: pip install hvac
"""
import logging
import time
from pathlib import Path
from typing import Optional
import hvac # pip install hvac
log = logging.getLogger(__name__)
VAULT_ADDR = "https://vault.internal.corp:8200"
VAULT_ROLE = "ai-agent-invoice-processor"
VAULT_DB_PATH = "database/creds/invoice-processor-role"
VAULT_K8S_AUTH_PATH = "auth/kubernetes"
K8S_SA_TOKEN_PATH = Path("/var/run/secrets/kubernetes.io/serviceaccount/token")
class VaultIdentityClient:
"""
Authenticates to HashiCorp Vault using Kubernetes workload identity
and retrieves dynamic database credentials.
Auth flow:
1. Read the Kubernetes service account token (short-lived, pod-bound)
2. POST it to Vault's Kubernetes auth endpoint
3. Vault calls the Kubernetes API to verify the token is valid and
the pod matches the configured role's bound_service_accounts
4. Vault issues a Vault token with a short TTL and specific policies
5. Use the Vault token to fetch dynamic database credentials
6. Vault creates a real, unique database user for this lease
7. Credentials are automatically revoked when the lease expires
"""
def __init__(
self,
vault_addr: str = VAULT_ADDR,
role: str = VAULT_ROLE,
token_path: Path = K8S_SA_TOKEN_PATH,
):
self.vault_addr = vault_addr
self.role = role
self.token_path = token_path
self._client: Optional[hvac.Client] = None
self._vault_token_expiry: int = 0
self._db_creds: Optional[dict] = None
self._db_creds_expiry: int = 0
def _authenticate(self) -> hvac.Client:
"""
Authenticate to Vault using the Kubernetes JWT auth method.
Returns an authenticated Vault client.
"""
jwt = self.token_path.read_text().strip()
client = hvac.Client(url=self.vault_addr)
response = client.auth.kubernetes.login(
role=self.role,
jwt=jwt,
mount_point=VAULT_K8S_AUTH_PATH,
)
# The Vault token has its own TTL (typically 1 hour for machine roles).
lease_duration = response["auth"]["lease_duration"]
self._vault_token_expiry = int(time.time()) + lease_duration
log.info(
"Vault auth successful: role=%s token_ttl=%ds policies=%s",
self.role,
lease_duration,
response["auth"]["policies"],
)
return client
def _ensure_authenticated(self) -> hvac.Client:
"""Return an authenticated Vault client, re-authenticating if needed."""
now = int(time.time())
# Re-authenticate if the Vault token expires within 5 minutes.
if self._client is None or self._vault_token_expiry - now < 300:
self._client = self._authenticate()
return self._client
def get_database_credentials(
self,
db_path: str = VAULT_DB_PATH,
force_refresh: bool = False,
) -> dict:
"""
Fetch dynamic database credentials from Vault.
Vault creates a unique PostgreSQL/MySQL user for each lease.
The user is automatically dropped when the lease expires.
This means no two agents ever share a database password,
and a compromised credential can be revoked instantly.
Returns: {"username": "...", "password": "...", "lease_duration": N}
"""
now = int(time.time())
# Return cached credentials if still valid (with 60s safety margin).
if (
not force_refresh
and self._db_creds
and self._db_creds_expiry - now > 60
):
log.debug("Using cached DB credentials (expires in %ds)", self._db_creds_expiry - now)
return self._db_creds
client = self._ensure_authenticated()
log.info("Requesting dynamic DB credentials from Vault path=%s", db_path)
response = client.secrets.database.generate_credentials(
name=db_path.split("/")[-1], # extract role name
mount_point="database",
)
lease_duration = response["lease_duration"]
self._db_creds = {
"username": response["data"]["username"],
"password": response["data"]["password"],
"lease_id": response["lease_id"],
"lease_duration": lease_duration,
}
self._db_creds_expiry = now + lease_duration
log.info(
"Dynamic DB credentials issued: username=%s lease_id=%s ttl=%ds",
self._db_creds["username"],
self._db_creds["lease_id"],
lease_duration,
)
return self._db_creds
def revoke_credentials(self) -> None:
"""
Explicitly revoke the current database credential lease.
Call this on agent shutdown to immediately invalidate the
database user rather than waiting for TTL expiry.
"""
if not self._db_creds or not self._client:
return
lease_id = self._db_creds.get("lease_id")
if lease_id:
try:
self._client.sys.revoke_lease(lease_id=lease_id)
log.info("Revoked Vault lease: %s", lease_id)
except Exception as exc:
log.warning("Failed to revoke lease %s: %s", lease_id, exc)
self._db_creds = None
Comparison and Tradeoffs
Identity Strategy Comparison Matrix
| Strategy | Credential Lifetime | Rotation | Attestation | Blast Radius | Ops Complexity | Scale Fit |
|---|---|---|---|---|---|---|
| Static API Keys | Never (manual) | Manual, painful | None | Full access until revoked | Very Low | <100 agents |
| SPIFFE/SPIRE SVIDs | 1-24 hours | Automatic | Workload-bound | Single agent, short window | High | 100-100,000+ |
| Kubernetes SA Tokens (projected) | 1 hour (default) | Automatic (kubelet) | Pod-bound | Single pod | Low (native K8s) | K8s-only workloads |
| AWS IAM Roles (EC2/EKS) | 15 min - 12 hours | Automatic (STS) | Instance/pod-bound | AWS account scope | Medium | AWS-only workloads |
| GCP Workload Identity | 1 hour | Automatic | Pod/SA-bound | GCP project scope | Medium | GCP-only workloads |
| Vault Dynamic Secrets | 5 min - 24 hours | Automatic | Vault policy | Single lease | High | Multi-cloud, polyglot |
| HashiCorp Vault + SPIFFE | 1-4 hours | Automatic | Workload-attested | Single workload, single lease | Very High | Enterprise multi-cloud |
When to Use Each Approach
Static API Keys are appropriate only for: external third-party APIs that do not support other auth methods, development and testing environments where the key is scoped to a sandbox, and legacy integrations where infrastructure investment is not justified. They should never be used for production AI agent infrastructure.
SPIFFE/SPIRE is the right choice when: you need a platform-agnostic identity layer that works across cloud providers, on-premises, and edge, you have complex workload topologies where a single agent orchestrates sub-agents across different runtimes, or you need strong workload attestation with policy enforcement at the identity layer.
Kubernetes Projected Service Account Tokens are appropriate when: all workloads run on Kubernetes, simplicity is paramount, and the identity needs are relatively uniform. This is the lowest-overhead option for pure Kubernetes deployments.
Cloud IAM Roles (AWS IAM, GCP Workload Identity) are appropriate when: all workloads run in a single cloud provider and you want to use that provider's native IAM system for authorization as well as authentication. The tradeoff is vendor lock-in and limited cross-cloud portability.
Vault Dynamic Secrets shine when: agents need credentials to multiple downstream systems (databases, message queues, cloud APIs) that are not themselves SPIFFE-aware. Vault acts as the credential broker, federating identity from SPIFFE or cloud IAM into system-specific dynamic credentials.
Performance and Scale Benchmarks
At 10,000 concurrent agents, each renewing its SVID once per hour, the SPIRE Server handles approximately 2.8 certificate signings per second. This is well within the capacity of a properly configured SPIRE Server (which can sustain 100+ signings/second per CPU core on modern hardware). However, there are two scale failure modes to design for.
The first is the cold start storm: if 10,000 agents start simultaneously (after a deployment or an outage), they all request SVIDs at once. This can saturate the SPIRE Server's signing capacity and the underlying CA. Mitigation: implement jittered startup delays (each agent waits a random 0-60 seconds before requesting its first SVID) and provision SPIRE Server in a horizontally scaled configuration with a shared upstream CA.
The second is the renewal storm: if all agents were issued SVIDs with the same expiry (e.g., all at the top of the hour), renewals cluster. Mitigation: SPIRE automatically adds jitter to renewal timing by renewing at a random point in the second half of the certificate's lifetime. Verify this behavior is enabled in your SPIRE configuration.
Production Considerations
Monitoring Identity Health
A machine identity system that is not monitored is a liability. Key metrics to track include: SVID issuance rate (alerts on sudden spikes indicating a provisioning storm or compromise), SVID rejection rate (alerts on sustained elevated rates indicating workload misconfiguration or attack attempts), certificate expiry distribution (ensure no certificates are within 10% of expiry without a pending renewal — this indicates a stuck rotation), and SPIRE Agent health per node (a failed SPIRE Agent blocks all identity requests from that node's workloads).
Integrate SPIRE's Prometheus metrics endpoint with your observability stack. Critical alerts: any agent that has not renewed its SVID within 2x the configured renewal threshold should be investigated immediately, as this indicates a renewal failure that will result in an expired certificate and service outage.
Detecting Compromised Identities
Compromised machine identity is harder to detect than compromised human identity because agents are expected to make many automated API calls. Behavioral baselines are essential. For each registered workload, establish: normal request rates per hour, typical geographic distribution of source IPs, standard set of downstream services accessed, and expected data transfer volumes.
Anomalies that warrant investigation: an agent identity appearing from an IP outside its expected CIDR range (possible credential theft), an agent identity making requests to services outside its normal access pattern (possible lateral movement after compromise), a surge in SVID requests from a single workload registration (possible identity harvesting attack), and any revoked identity appearing in access logs (indicates a revocation infrastructure failure).
Audit Trails and Compliance
SOC2 Type II and PCI-DSS both require comprehensive audit trails for non-human access to cardholder data and systems in scope. SPIRE Server logs every SVID issuance, including the workload selector that matched, the SPIFFE ID issued, and the timestamp. These logs must be shipped to a tamper-evident log store (e.g., AWS CloudTrail, Google Cloud Audit Logs, or a WORM-enabled S3 bucket) and retained for the period required by your compliance framework (typically 12 months for SOC2, 12 months for PCI-DSS).
For Vault dynamic secrets, enable the Vault audit log backend and ship to the same tamper-evident store. Every credential issuance and revocation event, with the requesting entity's Vault token identity and the policy that authorized the request, creates a complete chain of custody for every secret access.
For GDPR-adjacent considerations in AI agent deployments, note that SPIFFE IDs embedded in access logs may constitute metadata that links to personal data processing activities. Ensure your data retention and deletion policies account for these identity records.
Certificate Authority Resilience
The SPIRE Server's intermediate CA is a critical single point of failure. Configuration for production: deploy SPIRE Server in an active-standby configuration with a shared upstream root CA (HashiCorp Vault PKI, AWS Private CA, or a hardware HSM-backed CA). The upstream root CA should be air-gapped or HSM-backed for root key protection. SPIRE intermediate certificates should have a 24-hour lifetime with 12-hour renewal, so a SPIRE Server outage of up to 12 hours does not cause SVID expiry across the fleet (agents cache their SVIDs and can continue operating until the next renewal attempt fails).
Test your CA failover procedure quarterly. A CA outage during a deployment or incident response is a critical compounding failure.
Conclusion
Machine identity is the unglamorous infrastructure work that separates AI agent deployments that are secure and operable at scale from those that are one exposed environment variable away from a breach.
The core insight is this: the same automation that makes AI agents powerful — ephemeral, scalable, autonomous operation — is precisely what makes static credentials dangerous. Short-lived, attested, automatically rotated cryptographic identities are not a nice-to-have for large-scale AI agent infrastructure. They are a prerequisite.
The practical path forward depends on your current maturity. If you are running fewer than 100 agents and moving quickly, start with Kubernetes projected service account tokens — they are built in, require no additional infrastructure, and eliminate the worst static credential antipatterns. As your fleet grows toward 1,000 agents and you need cross-platform portability, invest in SPIRE. For dynamic credentials to databases and third-party APIs at any scale, add Vault as a credential broker layered on top of your primary identity system.
The investment in machine identity infrastructure pays dividends beyond security. Automatic credential rotation eliminates the operational toil of manual secret management. Workload attestation creates a reliable audit trail for compliance. Short-lived credentials reduce the blast radius of incidents that would otherwise cascade across your entire infrastructure.
The 45:1 ratio of machine-to-human API traffic will only grow as AI agent deployments mature. Building the identity infrastructure to manage it correctly — today, before the next incident — is the kind of work that does not show up in sprint reviews but absolutely shows up in post-incident reviews.
Start with attestation. Issue short-lived credentials. Automate rotation. Monitor everything. The machines are already talking to each other — make sure they are who they say they are.
*Next in the series: [Rate Limiting AI Agents: Protecting Your APIs at Scale](/blog/041-rate-limiting-ai-agents)*
Enjoyed this post? Follow AmtocSoft for AI tutorials from beginner to professional.
☕ Buy Me a Coffee | 🔔 YouTube | 💼 LinkedIn | 🐦 X/Twitter

No comments:
Post a Comment