
Level: Intermediate | Topic: API Security | Read Time: 6 min
APIs are the backbone of modern software. Every time you use a mobile app, load a dashboard, or connect two services together, there is an API behind the scenes handling the communication. But here is the problem: APIs are also the number one target for attackers.
In 2025, API-related breaches accounted for a significant portion of data leaks worldwide. Whether you are building a REST API, a GraphQL endpoint, or a microservice, securing your API is not optional. It is essential.
This guide walks through five critical API security practices that every developer should implement from day one.
1. Use Strong Authentication
Authentication is the front door of your API. If it is weak, everything behind it is exposed.
What to do:
- Use OAuth 2.0 or OpenID Connect for user-facing APIs.
- Use API keys combined with short-lived JWT tokens for service-to-service communication.
- Never pass credentials in URL query parameters. Always use headers.
- Rotate secrets and tokens on a regular schedule.
Why it matters: A leaked API key with no expiration is like leaving your house key under the doormat permanently. Short-lived tokens limit the blast radius of a compromise.
2. Implement Rate Limiting
Without rate limiting, a single bad actor can overwhelm your API with thousands of requests per second, degrading performance for everyone or launching brute-force attacks on authentication endpoints.
What to do:
- Set request limits per user, per IP, and per endpoint.
- Use sliding window or token bucket algorithms for fairness.
- Return
429 Too Many Requestswith aRetry-Afterheader. - Consider different tiers: stricter limits on login endpoints, more generous on read-only data.
Why it matters: Rate limiting protects your infrastructure from abuse, prevents credential stuffing attacks, and ensures fair access for all consumers of your API.
3. Validate All Input
Never trust data coming from the client. Every request parameter, header, and body payload is a potential attack vector.
What to do:
- Validate data types, lengths, and formats on every endpoint.
- Use allowlists rather than blocklists where possible.
- Sanitize inputs to prevent SQL injection, XSS, and command injection.
- Use a schema validation library (like Joi, Zod, or JSON Schema) to enforce structure.
Why it matters: Input validation is your first line of defense against injection attacks. The [OWASP Top 10](https://owasp.org/www-project-top-ten/) consistently ranks injection vulnerabilities among the most dangerous web security risks.
4. Encrypt Everything in Transit
If your API communicates over plain HTTP, anyone on the network path can read, modify, or intercept the data. This includes passwords, tokens, personal information, and business-critical payloads.
What to do:
- Enforce HTTPS (TLS 1.2 or higher) on all endpoints. No exceptions.
- Use HSTS headers to prevent downgrade attacks.
- Pin certificates in mobile apps where appropriate.
- Encrypt sensitive fields at the application layer for defense in depth.
Why it matters: TLS encryption ensures that data between the client and server cannot be read or tampered with in transit. Without it, API keys and user data travel in plaintext.
5. Log and Monitor API Activity
Security is not a one-time setup. You need visibility into how your API is being used and abused.
What to do:
- Log all authentication attempts (successes and failures).
- Track unusual patterns: spikes in 4xx errors, requests from unexpected geolocations, abnormal payload sizes.
- Set up alerts for anomalies using tools like ELK Stack, Datadog, or AWS CloudWatch.
- Retain logs for compliance and forensic analysis.
Why it matters: If a breach happens, logs are how you detect it, understand the scope, and respond. Without logging, you are flying blind.
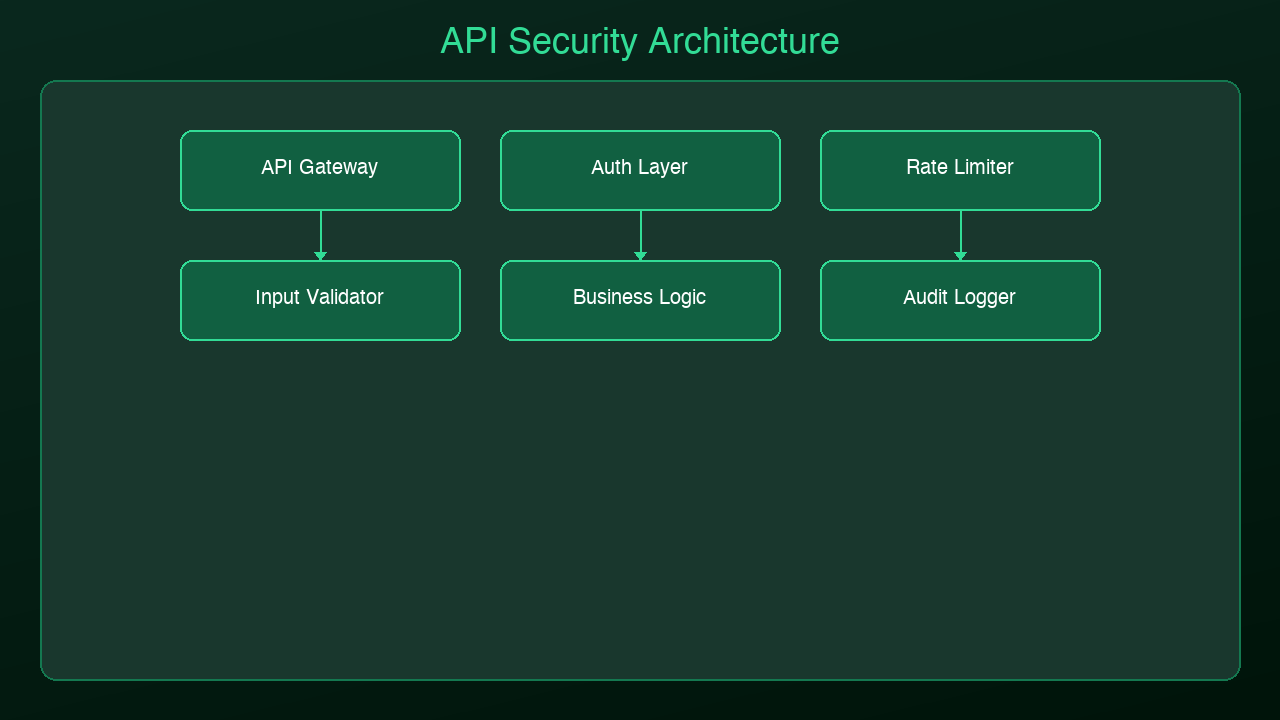
Putting It All Together
These five practices form a security baseline that every API should have before going to production:
1. Authenticate every request with strong, short-lived credentials.
2. Rate limit to prevent abuse and protect infrastructure.
3. Validate inputs to stop injection attacks at the boundary.
4. Encrypt in transit so data cannot be intercepted.
5. Log and monitor to detect and respond to threats.
Security is not a feature you add later. It is a design principle you build in from the start.
Next Steps
- Review the [OWASP API Security Top 10](https://owasp.org/www-project-api-security/) for a comprehensive threat model.
- Audit your existing APIs against these five practices.
- Set up automated security scanning in your CI/CD pipeline.
If you found this useful, follow AmtocSoft for more practical guides on security, performance, AI, and software engineering. From beginner-friendly explainers to professional-grade deep dives, we cover every level.
Sources & References:
1. OWASP — "API Security Top 10" (2023) — https://owasp.org/www-project-api-security/
2. OWASP — "Top 10 Web Application Security Risks" — https://owasp.org/www-project-top-ten/
3. Auth0 — "OAuth 2.0 Overview" — https://auth0.com/intro-to-iam/what-is-oauth-2
4. Cloudflare — "What Is Rate Limiting?" — https://www.cloudflare.com/learning/bots/what-is-rate-limiting/
*Published by AmtocSoft | amtocsoft.blogspot.com*
*Level: Intermediate | Topic: API Security*
Enjoyed this post? Follow AmtocSoft for AI tutorials from beginner to professional.
☕ Buy Me a Coffee | 🔔 YouTube | 💼 LinkedIn | 🐦 X/Twitter

No comments:
Post a Comment