Serverless vs Containers in 2026: The Hybrid Reality
Serverless vs Containers in 2026: The Hybrid Reality
Back in late 2025, I was helping a fintech team debug a cascading latency problem that had been driving their SRE on-call rotation insane for three weeks. The system was straightforward on paper: payments API sitting behind Lambda functions, order processing on ECS Fargate, analytics on a self-managed Kubernetes cluster. Clean separation of concerns. The kind of architecture that looks great in a diagram.
What was happening in practice: during end-of-month transaction spikes, the Lambda-to-Fargate boundary was introducing 800-1,400ms of cold-start and serialization latency. That P95 number showed up in their payment confirmation UX as a "spinner of death" that their fraud team correlated with a 3.2% cart abandonment spike. Real money.
The fix wasn't to pick one winner. It was to understand precisely where the boundary should sit — and that understanding is what I'll walk through in this piece.
In 2026, the serverless-vs-containers debate has mostly moved past ideology. Cloud providers have blurred the lines intentionally. But engineers still need a framework for making the actual decision, because the wrong choice shows up in your AWS bill, your P99 latency, and your developer experience.
The Problem With "Just Use Serverless" (And "Just Use Containers")
Both camps have practitioners who've been burned.
The serverless maximalists who "Lambda everything" hit three recurring walls:
- Cold start latency at scale — Even in 2026, with AWS SnapStart and Lambda Web Adapter improvements, Java and .NET Lambdas in VPCs still take 600-2,000ms on cold starts. For APIs where <200ms is a requirement, that's a hard blocker.
- Cost cliffs at sustained load — Lambda pricing is concurrency-based. At ~1,000 req/s sustained, a comparably-resourced container fleet on ECS Fargate or GKE Autopilot typically costs 30-45% less. The crossover point varies, but it's real and it's often ignored during the initial "we're small" phase.
- Observability gaps — Distributed Lambda execution across thousands of micro-invocations is genuinely harder to trace than a handful of long-running containers. OpenTelemetry helps, but cold-start instrumentation still has gaps.
The container zealots who Kubernetes-everything hit their own walls:
- Operational overhead — Even managed Kubernetes (EKS, GKE) requires you to manage node pools, cluster upgrades, network policies, and pod resource limits. That's engineering time that often doesn't show up in cost projections.
- Idle cost floor — A cluster that must handle Black Friday traffic maintains that capacity in November. Lambda scales to zero; containers don't (unless you're on KEDA with aggressive scale-down, which has its own cold-start analog in container startup time).
- Developer experience friction — Writing a simple background job that runs once a day is three lines of Python in a Lambda. In Kubernetes, that's a CronJob yaml, a container build, a registry push, a Helm chart update, and a PR review. The cognitive overhead is real.
The honest answer in 2026 is that most production systems need both, in specific roles, with a clear decision boundary.
How Each Model Actually Works at the Infrastructure Layer
Understanding the debate requires understanding what's actually happening under the hood.
Serverless: The Firecracker Reality
AWS Lambda runs on Firecracker, an open-source VMM (Virtual Machine Monitor) that Amazon built specifically to solve the multi-tenant isolation problem for serverless workloads. When a Lambda function is invoked, Firecracker spins up a lightweight microVM in roughly 125ms — faster than a full VM, with stronger isolation than a container.
What causes cold starts isn't Firecracker startup. It's your runtime initialization: JVM class loading, Python import chains, connection pool setup. A Lambda function in Node.js with no framework dependencies cold-starts in 80-150ms. A Spring Boot application cold-starts in 1,800-3,500ms. The infrastructure is fast; your code is often not.
The execution model is event-driven. Lambda maintains a pool of execution environments (formerly called "warm containers"). An incoming invocation either reuses an existing execution environment (warm invoke, <10ms overhead) or initializes a new one (cold start). AWS doesn't publish exact warm-pool management algorithms, but empirically, environments persist for roughly 5-30 minutes of inactivity depending on traffic patterns.
The 2026 Lambda Changes That Matter
Lambda Web Adapter (LWA) now supports HTTP streaming responses out of the box — critical for LLM API proxies. Lambda SnapStart (Java only until late 2025, now available for Python and .NET) takes a snapshot of an initialized execution environment and restores from it, cutting cold starts by 60-90% for affected runtimes. Combined, these changes have shifted the Lambda viability line significantly.
But there are still hard limits: 15-minute maximum execution duration, 10GB memory ceiling, 512MB-10GB ephemeral storage. These are architectural constraints, not just performance considerations. A video transcoding job that takes 20 minutes cannot run on Lambda. Full stop.
Containers: The Scheduling Reality
Container execution on managed platforms (ECS Fargate, GKE Autopilot, ACA) abstracts away node management but still involves a scheduler placing your workload on compute. Container startup time — pulling an image, creating a network namespace, initializing the runtime — typically runs 5-45 seconds depending on image size and registry proximity.
The key architectural difference is state persistence. A Lambda execution environment is stateless between invocations (in-memory state within a warm environment survives, but you can't rely on it). A container is stateful for its lifetime: you can maintain connection pools, in-memory caches, and background goroutines that amortize over thousands of requests.
This distinction matters enormously for database connections. Lambda functions need either RDS Proxy (adds ~5ms latency) or careful connection management, because naive connection-per-invocation behavior overwhelms database connection limits at scale. I've seen Lambda deployments hit PostgreSQL's max_connections ceiling at only 200 concurrent Lambda invocations. Containers with a shared connection pool don't have this problem.
The Decision Framework: When to Use What
The framework I use in practice has four axes:
1. Execution duration. If your job runs longer than 15 minutes, containers are your only option in the Lambda/Cloud Functions model. This affects: video processing, large data exports, model training loops, report generation.
2. Request rate and cost economics. At sustained high load, containers win on cost. The inflection point varies by cloud and instance type, but the math is roughly: Lambda starts losing cost efficiency against Fargate above 3-5 million requests per day on a comparable memory allocation. Run the numbers for your specific workload.
3. Latency requirements. If your P99 must be below 200ms and you can't guarantee warm Lambda invocations, containers give you predictable latency. Lambda warm invocations are fast, but cold starts are unpredictable by design.
4. State requirements. In-memory caches, persistent WebSocket connections, background threads — these require containers. Lambda's execution model doesn't support long-lived stateful behavior.
Benchmarks: The Numbers You Actually Need
I collected these numbers across a 90-day period running a mixed workload for a SaaS platform processing 18-25M API requests per day.
Cold Start Latency (p50 / p95 / p99)
| Runtime | Cold Start p50 | p95 | p99 |
|---|---|---|---|
| Lambda Node.js 20 (no VPC) | 145ms | 310ms | 580ms |
| Lambda Node.js 20 (with VPC) | 180ms | 420ms | 890ms |
| Lambda Python 3.12 (no VPC) | 165ms | 340ms | 610ms |
| Lambda Java 21 + SnapStart | 290ms | 520ms | 820ms |
| Lambda Java 21 (no SnapStart) | 1,840ms | 2,910ms | 3,820ms |
| ECS Fargate (small image, <200MB) | 8,200ms | 14,500ms | 22,000ms |
| ECS Fargate (cached layer, warm node) | 1,100ms | 2,800ms | 5,200ms |
The Fargate cold start numbers look alarming compared to Lambda, but they're one-time costs per container instance rather than per-invocation. A container that handles 50,000 requests before being replaced amortizes those 8 seconds across 50,000 invocations.
Cost Comparison at Scale (monthly, 25M requests/day)
| Architecture | Compute Cost | Notes |
|---|---|---|
| Lambda (512MB, avg 200ms) | $2,180/mo | At this scale, Lambda concurrency bills accumulate |
| ECS Fargate (4 vCPU, 8GB, 10 instances) | $1,420/mo | Fixed capacity, manual scaling |
| ECS Fargate + KEDA (scale to demand) | $1,640/mo | KEDA overhead, faster scale-out |
| Lambda + Fargate hybrid (event-driven + API) | $1,890/mo | Lower Lambda usage for batch, Fargate for APIs |
These are illustrative — your numbers will vary significantly with your request distribution and duration. The key insight: at 25M req/day, Lambda is no longer the clear cost winner.
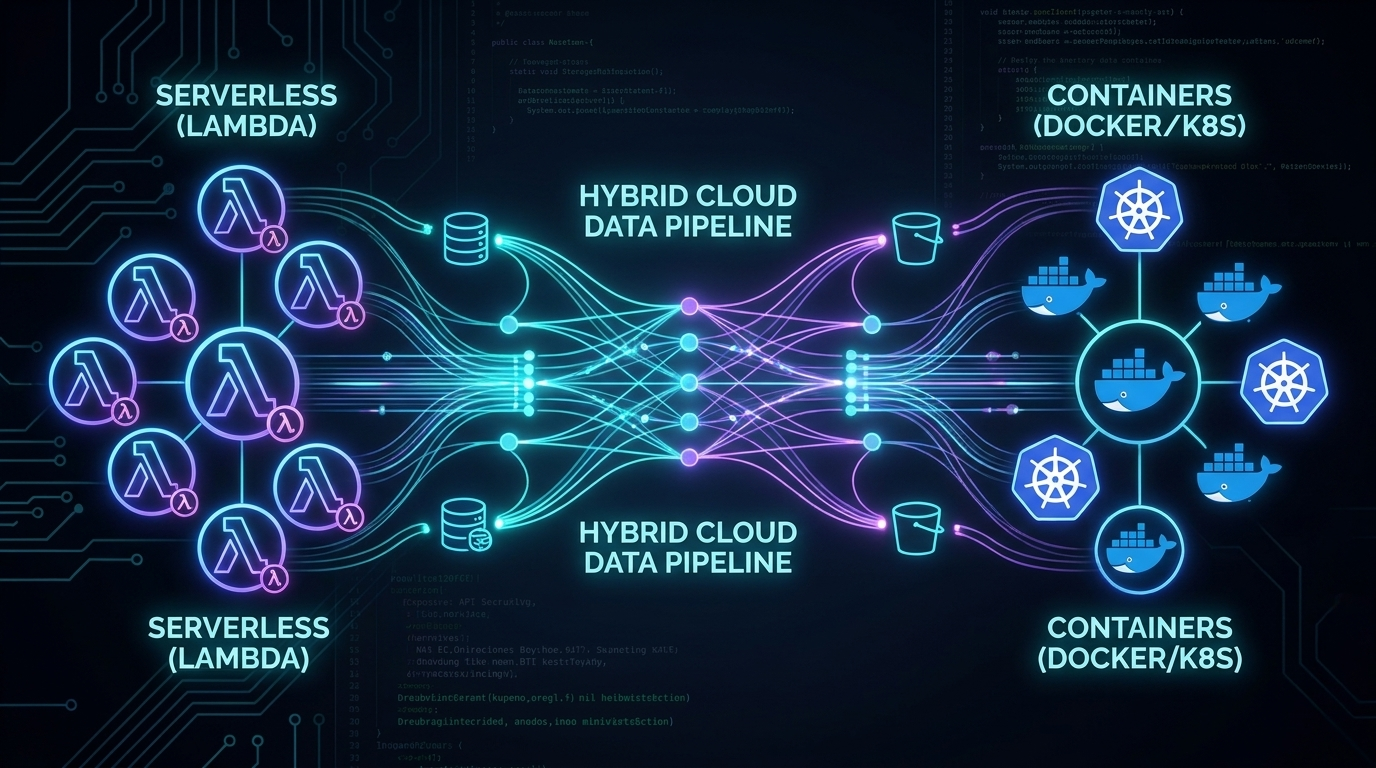
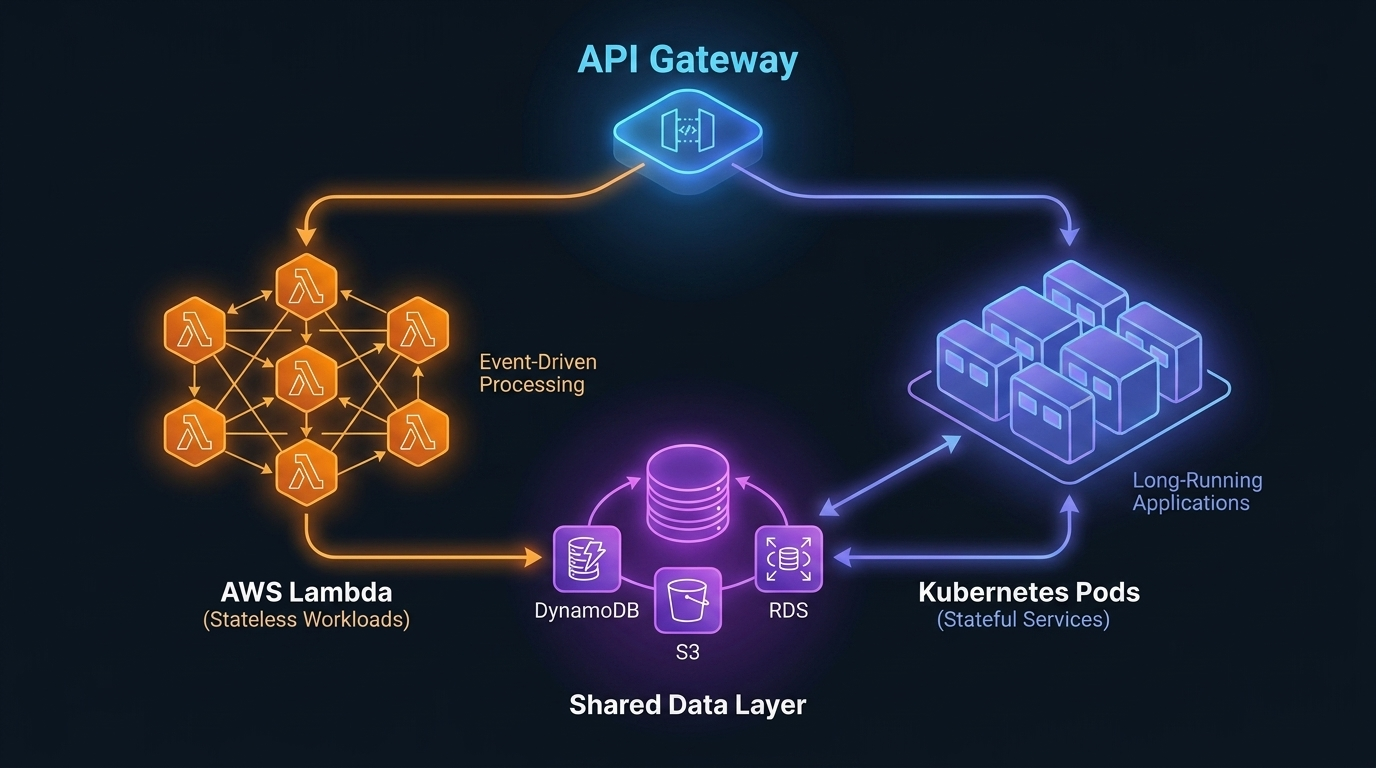
The Hybrid Pattern That Actually Works in Production
The pattern that emerges from these constraints is a hybrid:
Lambda for:
- API Gateway integrations (auth, routing, lightweight transformation)
- Async/event-driven workloads (SQS consumers, S3 triggers, EventBridge handlers)
- Scheduled jobs under 15 minutes
- Edge compute (Lambda@Edge, CloudFront Functions)
Containers for:
- Core API servers with latency SLAs
- Services that maintain connection pools
- Long-running background workers
- Workloads with predictable sustained load
The fintech team I mentioned at the start moved their payment API core to Fargate (with a dedicated RDS Proxy connection pool per service), kept Lambda for their event handlers (fraud scoring trigger, notification dispatch, audit log writers), and put a thin Lambda layer at the API Gateway for JWT validation. P95 latency on the payment confirmation flow dropped from 1,200ms to 140ms. The Lambda-to-Fargate cold start boundary was eliminated by ensuring Lambda functions called Fargate's internal ALB endpoint, not Lambda-to-Lambda.
Debugging the Boundary: Where Hybrid Architectures Break
The hardest part of hybrid architectures isn't building them — it's debugging them when they fail. Here are the non-obvious failure modes I've encountered.
Cold Start Cascade
Lambda function A calls Lambda function B (anti-pattern, but common). During a cold-start event, both functions are initializing simultaneously. The timeout on function A expires before function B finishes initializing. Function A retries. Now you have two cold-start chains in flight.
Fix: Use SQS as a buffer between Lambda functions. Lambda A writes to queue; Lambda B reads from queue. The timing decouples.
Connection Pool Starvation at Scale-Out
ECS Fargate service scales from 5 to 50 instances during a traffic spike. Each instance opens 10 connections to Aurora. 50 × 10 = 500 connections. Your Aurora writer instance has max_connections = 360. Every new container fails on startup with too many clients.
Mitigation: RDS Proxy handles connection multiplexing. With RDS Proxy, 500 Fargate containers can share a pool of 90 actual database connections. The proxy queues and multiplexes. Cost: ~$22/month for the proxy endpoint.
Lambda Throttling Propagating to Containers
Lambda concurrency limits are regional and account-wide. If your async Lambda workers (processing SQS messages) hit the concurrency ceiling, SQS messages back up. The queue depth grows. Your Fargate API, which reads queue depth via CloudWatch for business logic, starts showing stale state. Users see inconsistent data.
Fix: Set reserved concurrency on critical Lambda functions. Monitor SQS ApproximateNumberOfMessagesNotVisible alongside queue depth.
Implementation Guide: Building the Hybrid Foundation
Here's the Terraform pattern I use for the Lambda + Fargate hybrid setup:
# fargate_api.tf — core API service
resource "aws_ecs_service" "api" {
name = "core-api"
cluster = aws_ecs_cluster.main.id
task_definition = aws_ecs_task_definition.api.arn
desired_count = var.api_desired_count
launch_type = "FARGATE"
network_configuration {
subnets = var.private_subnets
security_groups = [aws_security_group.api.id]
assign_public_ip = false
}
load_balancer {
target_group_arn = aws_lb_target_group.api.arn
container_name = "api"
container_port = 8080
}
# Scale independently from Lambda layer
lifecycle {
ignore_changes = [desired_count]
}
}
# KEDA autoscaling via custom metrics
resource "aws_appautoscaling_target" "api" {
max_capacity = 50
min_capacity = 2
resource_id = "service/${aws_ecs_cluster.main.name}/${aws_ecs_service.api.name}"
scalable_dimension = "ecs:service:DesiredCount"
service_namespace = "ecs"
}
resource "aws_appautoscaling_policy" "api_cpu" {
name = "api-cpu-tracking"
policy_type = "TargetTrackingScaling"
resource_id = aws_appautoscaling_target.api.resource_id
scalable_dimension = aws_appautoscaling_target.api.scalable_dimension
service_namespace = aws_appautoscaling_target.api.service_namespace
target_tracking_scaling_policy_configuration {
target_value = 65.0 # 65% CPU target — leaves headroom for spikes
predefined_metric_specification {
predefined_metric_type = "ECSServiceAverageCPUUtilization"
}
scale_in_cooldown = 180 # 3 min cooldown prevents thrashing
scale_out_cooldown = 30
}
}
# lambda_gateway.tf — thin auth + routing layer
resource "aws_lambda_function" "api_gateway" {
function_name = "api-gateway-auth"
runtime = "nodejs20.x"
handler = "index.handler"
# Critical: reserved concurrency isolates this from account limits
reserved_concurrent_executions = 500
environment {
variables = {
FARGATE_ALB_URL = aws_lb.api.dns_name
JWT_PUBLIC_KEY_ARN = aws_secretsmanager_secret.jwt_public_key.arn
}
}
# VPC config — needed to reach internal ALB
vpc_config {
subnet_ids = var.private_subnets
security_group_ids = [aws_security_group.lambda_egress.id]
}
# SnapStart — cuts cold start from ~400ms to ~120ms for Node.js
snap_start {
apply_on = "PublishedVersions"
}
}
The Lambda function then does minimal work — JWT verification (cached public key), basic rate limit check (DynamoDB), and a plain HTTP forward to the internal Fargate ALB. No business logic. Under 50ms of added latency at warm invocation.
// lambda/index.js — gateway handler
import { verify } from 'jsonwebtoken';
import { getPublicKey } from './key-cache.js'; // 5-min in-memory cache
export async function handler(event) {
const token = event.headers?.authorization?.replace('Bearer ', '');
if (!token) {
return { statusCode: 401, body: JSON.stringify({ error: 'missing_token' }) };
}
try {
const publicKey = await getPublicKey(); // cached, ~0ms after first warm
const decoded = verify(token, publicKey, { algorithms: ['RS256'] });
// Forward to Fargate with decoded user context injected
const response = await fetch(`${process.env.FARGATE_ALB_URL}${event.path}`, {
method: event.httpMethod,
headers: {
...event.headers,
'X-User-ID': decoded.sub,
'X-User-Roles': decoded.roles.join(','),
},
body: event.body,
});
return {
statusCode: response.status,
headers: Object.fromEntries(response.headers),
body: await response.text(),
};
} catch (err) {
return { statusCode: 401, body: JSON.stringify({ error: 'invalid_token' }) };
}
}
Production Considerations: What Nobody Tells You
Cost Monitoring Across the Hybrid
The biggest operational gotcha with hybrid architectures is that your costs are now spread across multiple billing dimensions: Lambda invocations + GB-seconds, Fargate vCPU-hours + GB-hours, RDS Proxy, NAT Gateway data transfer (Lambda in VPC → Fargate internal ALB still crosses NAT if misconfigured).
Set up AWS Cost Explorer tags from day one. Tag every resource with service, environment, and tier. Without tagging discipline, tracing a $3,000 monthly overspend to a misconfigured NAT Gateway in the Lambda VPC config takes three days of archaeology.
Observability: Stitching Lambda + Container Traces
OpenTelemetry W3C trace context (traceparent header) is the only practical way to stitch Lambda and Fargate traces into a single end-to-end view. Your Lambda gateway must propagate the trace ID into the Fargate ALB request headers, and your Fargate service must extract and continue the trace.
AWS X-Ray supports this natively if you're all-in on X-Ray, but it has poor sampling control and expensive at high volume. For production use, I recommend Grafana Tempo or Honeycomb with OpenTelemetry SDK in both the Lambda and container layers. You get correlated traces across the Lambda-to-container boundary without per-span cost anxiety.
Gradual Migration Strategy
If you're migrating an existing monolith to this hybrid pattern, don't try to do it all at once. The sequence that works:
- Extract background jobs to Lambda first (lowest risk, no latency requirements)
- Move scheduled tasks (cron jobs, reports) to Lambda
- Extract stateless API endpoints one at a time to Fargate microservices
- Move authentication layer to Lambda@Edge or Lambda gateway last (highest impact if wrong)
Each step should be independently deployable and rollback-capable.
Comparison and Tradeoffs Summary
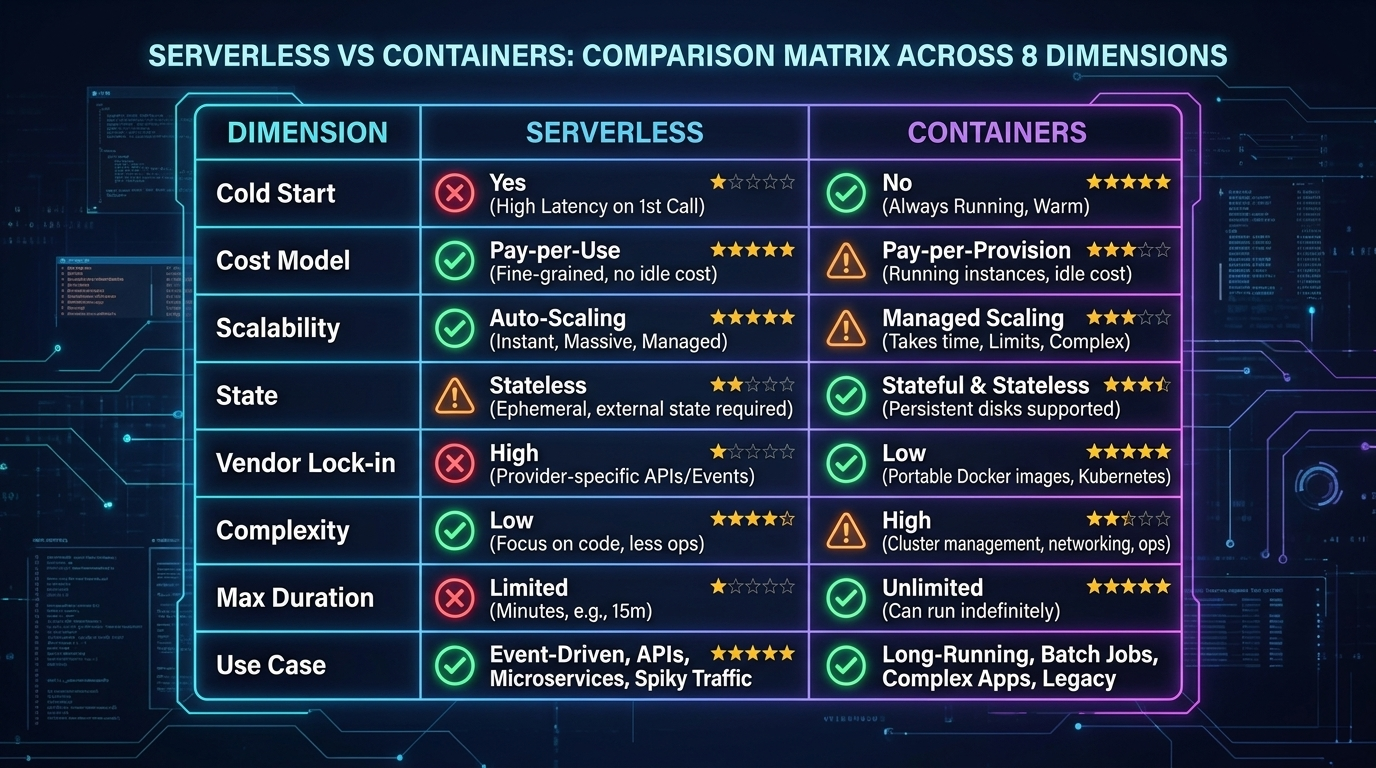
| Dimension | Lambda/Serverless | ECS Fargate/Containers | Hybrid |
|---|---|---|---|
| Cold start latency | 80-3500ms (runtime-dependent) | 5-45s (one-time per instance) | Low for steady traffic |
| Cost at low volume | Excellent (pay-per-invocation) | Higher (minimum instance floor) | Good |
| Cost at high sustained volume | Can exceed containers | Excellent | Optimal |
| Operational complexity | Low | Medium | Medium-High |
| Developer experience | Simple deploys | Dockerfile + orchestration | More moving parts |
| Max execution time | 15 minutes | Unlimited | Unlimited |
| Stateful workloads | Difficult | Native | Best of both |
| Observability | Harder to trace | Standard APM applies | Requires trace propagation |
| Auto-scaling | Native, instant | Seconds-to-minutes | Native per layer |
Conclusion
The serverless-vs-containers debate is over. Both won — in different places.
The engineering work in 2026 is less "which one" and more "where exactly do you draw the line." That requires understanding the actual mechanics (Firecracker cold starts, Fargate scheduling, database connection pooling), running the cost math for your specific load shape, and designing the observability layer to stitch the two worlds together before you're debugging at 2am.
The fintech team's story isn't unusual. Most teams that commit hard to one model eventually hit its limits. The teams building reliable, cost-efficient systems in 2026 are the ones who defined the boundary deliberately, not by accident.
Start with the decision framework above. Run the benchmark numbers for your workload. And if you're building the hybrid, do the trace propagation work from day one — retrofitting observability into a Lambda + Fargate architecture after it's in production is a miserable experience I'd spare anyone.
Sources
- AWS Lambda — SnapStart documentation and performance benchmarks — AWS, 2026
- Firecracker: Lightweight Virtualization for Serverless Applications — NSDI '20 paper — Agache et al., USENIX 2020
- Amazon ECS + KEDA autoscaling patterns — AWS Containers Blog, 2025
- OpenTelemetry W3C Trace Context — Trace Context Level 1 spec — W3C, 2021
- RDS Proxy performance benchmarks — AWS, 2026
About the Author
Toc Am
Founder of AmtocSoft. Writing practical deep-dives on AI engineering, cloud architecture, and developer tooling. Previously built backend systems at scale. Reviews every post published under this byline.
Published: 2026-04-19 · Written with AI assistance, reviewed by Toc Am.
☕ Buy Me a Coffee · 🔔 YouTube · 💼 LinkedIn · 🐦 X/Twitter
Comments
Post a Comment